One key to deploy openclaw
In general, seo is divided into white hats and black hats. The seo black hat is the method by which people who swim through the search engine algorithms, using hacking techniques and some of the search engine edge algorithms, are able to access traffic or ranking quickly。
While seo traffic hijacking is one of the black hat techniques, the most basic methods of traffic hijacking have been duly completed by the search engine k, which analyses and shares high-level applications of seo traffic hijacking and looks at live cases where the site is not currently punished by the search engine。
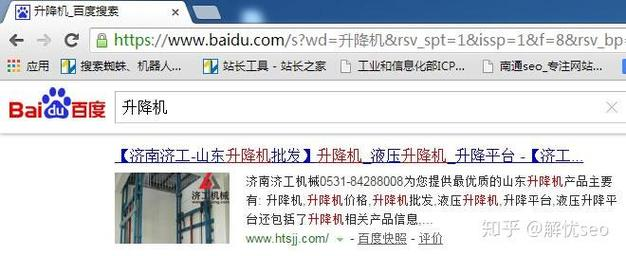
1. Open 100 degrees, search the elevator and find the first-ranking website, as illustrated below。
Seo traffic hijacking cases (figure 1)

2. After clicking on this site, did you find anything unusual? As shown in the figure below。
Seo traffic hijacking cases (figure 2)
Abnormal: we're just a normal click, not doing anything else, before the 100-degree search of the elevator automatically jumped into a keyword hydraulic lift, and the search results became the result of a station search on this domain name!
Seo traffic hijacking cases (figure 3)
That's where the black hat seoer is, and it's hard to detect this slight change without our careful observation。
Why is this happening? Seems like he's got it under his control. After a careful analysis of the source code of his website, it turns out that at the bottom, a js document was quoted, and then clicked in, which was a simple result of the expansion of seo traffic hijacking technology。
This js can perform the following functions: when users click on the site from major search engines (e. G., 100 degrees, 360 degrees), it can redirect previous pages to any page and access the site in other ways. Interested partners can study it。
Using this black hat technology, combined with the flow stations in your hands, we can easily and quietly hijack the flow of users for marketing or seo purposes. But after all, it's a black hat technology, the search engine is improving every day, and the black hat has a short life cycle, so it's not recommended。
The black hat seo has the advantage of a black hat seo, but the disadvantages are also obvious, and for a normal commercial website and most individual websites, good content, normal optimization and attention to user experiences are the path to success。
The author of this paper, yuzhmorgeologiya (www. Banzhuseo. Com), is the author of this article, which was first issued as a5, and is reproduced as indicated。
To apply for entrepreneurial coverage and share good ideas. Come here to explore new opportunities for entrepreneurship




