I. What do we need to study in company security engines
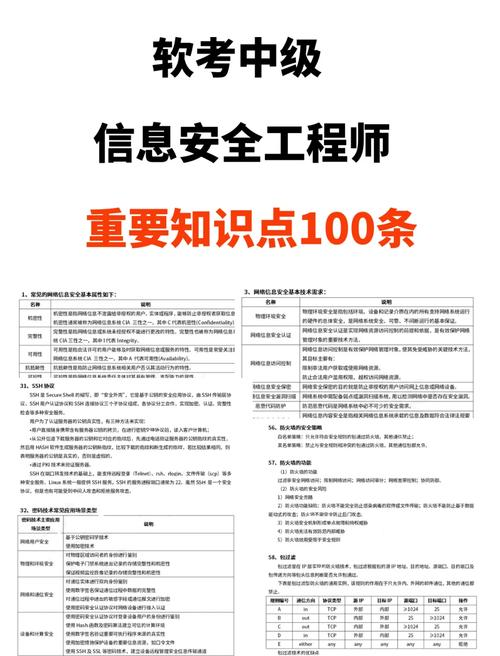
Cybersecurity engineers, fully known as network information security engineers, are those who, in accordance with the information security management system and standards, prevent hacking, analyse and guard against hacking, conduct security system construction and security technical planning, day-to-day maintenance management, information security checks and system log checks through the use of various safety products and technologies, such as firewalls, anti-virus, ids, pki, offensive techniques, etc. Cybersecurity engineers are a new type of profession in which they are required to obtain relevant qualifications. They do not have qualifications, qualifications, age requirements, etc., but they still need to have a limited pool of computer technology and network security-related knowledge, which requires a wide range of learning, including: 1. Cybersecurity techniques, including port, service gap scanning, program gap analysis detection, competency management, intrusion and assault analysis tracking, web penetration, viral horse protection, etc. 2. Programming languages: knowledge of one or more programming languages, such as php, shell, perl, python, c, c++. 3. The configuration and use of network security equipment. Knowledge related to cybersecurity: e. G. Tcp/ip protocol, information storage and transmission security。
What is the content of cybersecurity training
Training in cybersecurity, training in cybersecurity for those who, by definition, want to engage in cybersecurity, such as network operators, aims and means, inter alia, to disseminate new developments, theories and information on cybersecurity developments to those trained, to develop the skills and levels of training participants in cybersecurity, to ensure that participants fully integrate their knowledge of cybersecurity, and to improve the skills and levels of cybersecurity protection. The content of the training on cybersecurity is not fixed and different training courses may be selected depending on the training needs, actual situation, target level, etc. The regular training will typically consist of four parts: one and one: network and system security, including route exchange techniques, firewall/ips/ids, data package analysis, windows and linux systems, system security enhancements, enterprise network system security architecture design, etc. Part ii: web security, consisting of web infrastructure, web site infrastructure, python infrastructure and reptiles, and web attack. Part iii: infiltration testing, which includes information gathering, social engineering, the use of loopholes, penetration power, internal penetration, malicious code analysis, reverse. 4. Part iv: security services, including legislation and regulations, insurance 2. 0, risk assessment, emergency response, evidence collection, etc。
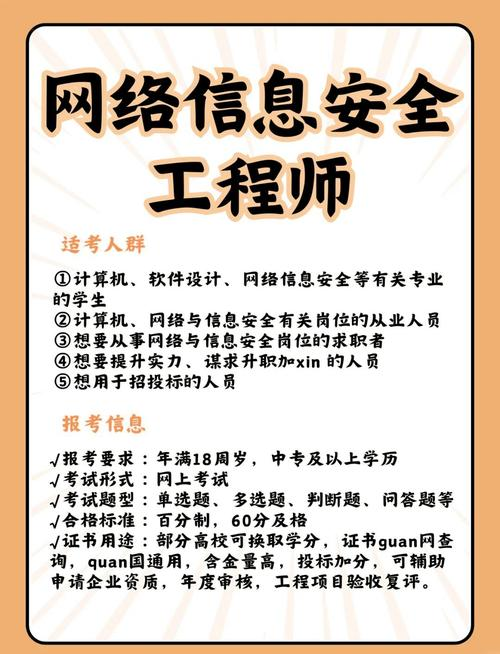
Iii. Qualifications for cybersecurity
Cybersecurity is an internet company engaged in cybersecurity that provides solutions for the general public. The qualifications required by cybersecurity are mainly those of information security services, and it is a qualification for the provision of security services by information security services, including legal status, resource status, level of management and technical capability, with a total of eight directions, namely: security integrated services, security transport services, risk assessment services, emergency handling services, software security development services, disaster backup and restoration services, industrial control security services, network security audit services. There are also different types of cybersecurity companies, and different cybersecurity companies require different qualifications. If you need the services of a cybersecurity company, you can start with the top ten brands。
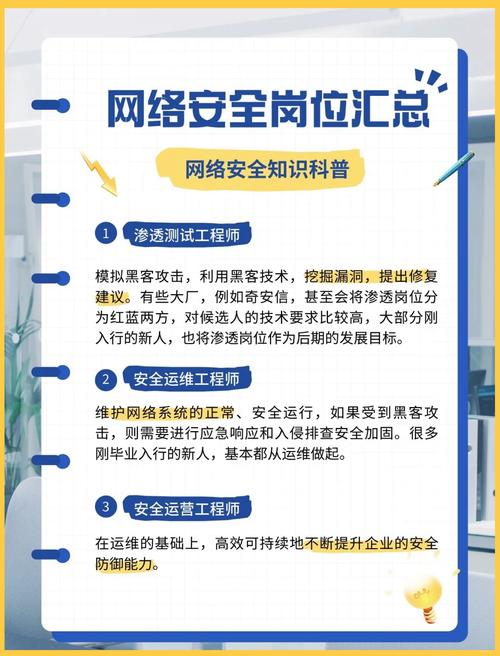
Iv. Employment problems for company security
With the development of networks, the importance of cybersecurity has grown, and the prospects for employment in cybersecurity professions have been broader, mainly due to: one, the great demand for talent: the fact that enterprises are not easily recruiting suitable cyber-security personnel, the large number of job-seekers whose professional skills are limited to meet the demands of the enterprise, the large shortage of new types of network personnel, and the fact that 27 per cent of industry growth has led to an annual deficit of 300,000 network personnel, with high pay and benefits inevitable. 2. High ceilings for the development of internet security: after graduation, the focus is on the development and maintenance of enterprise information, including technical and managerial work, which is relatively stable, and which tends to grow as the experience of the project grows and the industry background is better understood. 3. High value added potential: taking advantage of the core enterprise network architecture, security technologies, has an irreplaceable competitive advantage. The value of the profession increases with experience and maturity of the project。




