The integrated urban orbital traffic control system, which guarantees the proper functioning of the subway, plays an important role in ensuring the safety of trains, passengers and staff, thus contributing to the improvement of the quality of orbital traffic and the efficiency of integrated operations. The present paper provides a comprehensive survey and detailed analysis of the safety of the network of the integrated subway control system (imms) in accordance with the level of protection requirements, in conjunction with the operational system, and proposes an information security system that meets both operational and level ii protection requirements。
Below is an extract from the original programme
Introduction
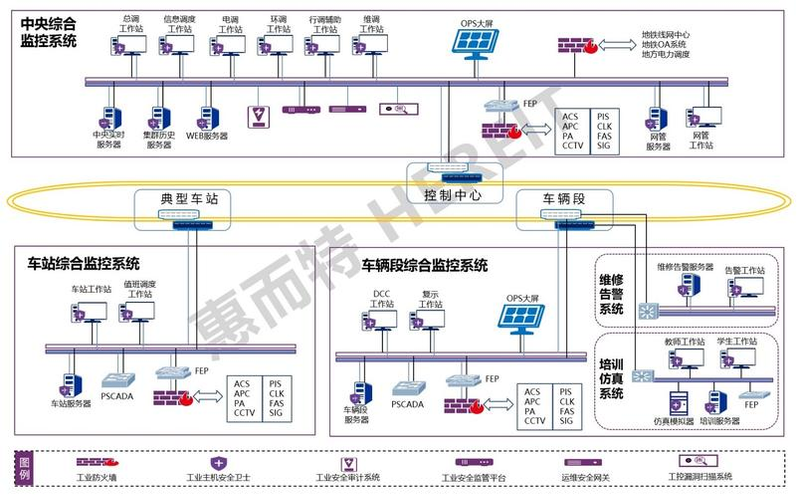
The integrated urban orbit traffic control system is a layered, distributed computer integrated system for the monitoring of electrical equipment in urban orbital traffic lines. The integrated control system (ims) has achieved support vehicle command, monitoring and management of mechanical and electrical equipment, disaster prevention and security, passenger services, system maintenance management and energy consumption management functions and is coordinated with the systems。
The ims consists of a central monitoring system, a station-level monitoring system and a backbone network, which connects the ims and station-level monitoring systems to the entire ims system. The station-level integrated surveillance system is operated on a stand-alone basis in the event of a failure of the central level integrated control system。
The integrated monitoring system (imms) is structured in an integrated and interconnected manner, with the full functionality of ims being achieved by ims as part of the integrated monitoring system (imms), which operates independently and has its own complete system structure, which interacts with ims information through external interfaces to achieve information interoperability, sharing and connectivity control。
The ims targets include electricity monitoring, environmental and equipment monitoring, fire alarm systems, train auto-monitoring systems, screen doors, flood control doors, video surveillance systems, broadcasting systems, passenger information systems, automated ticket control systems, door-barrel systems and clock systems。
In accordance with the responsibilities and requirements of hierarchical management of urban orbital traffic operations, the monitoring and management functions of ims are divided into central, station and field levels. Central-level integrated monitoring provides real-time collection and processing of data on the status, parameters of the objects being monitored on a line. The integrated station-level monitoring system provides operational control of the persons under control in the jurisdiction。
Needs analysis
Technology needs analysis
Cyber border security
Border access to network communication systems within ims is mainly used for integrated or interconnected systems interfaced with ims, which directly exposes borders to multiple subsystems, complex environments and high security risks, and multiple cyberattacks and traffic attacks against websites are common security threats. Therefore, the border should be secured by strict security safeguards to protect the entire metro system from intrusion。
End behaviour management
The security of terminal equipment is the most problematic security issue for network managers because of the decentralized deployment of end equipment and the uneven computer level of operators. Terminal leaks, unauthorized access and internal attacks all pose a threat to data centre security. Patch management of various terminals and server systems is also an important issue。
Terminal antivirus
The virus is the most dangerous hazard to the computational environment, especially the worm virus, and is rapidly spreading to other subnets, which can significantly capture the very limited bandwidth of normal operations, causing a severe decline in network performance and even disruption of network communications, seriously affecting normal operations。
Network intrusion detection
The attacks are not only from recognized external networks, but also from within. Through the deployment of security measures, various attacks against information systems, such as viruses, wooden horses, spy software, suspected codes, port scanning and dos/ddos, can be actively prevented, and can be protected from attack against operational system loopholes。
Application of security management
From a user's perspective, the proper functioning of its business systems is a central issue, while the ability of business systems to implement good control management is one of the key factors. There is therefore a need for technical means to monitor the status of the application system in a comprehensive manner, to provide an overview of the operational environment, to implement proactive monitoring, to conduct operational trend analysis and to identify problems in a timely manner。
Security management needs analysis
“technology integration”, in addition to information security technical measures to control information security threats, is an essential tool for security management measures. A sound security management system ensures the effective implementation of security precautions, secures the network system, complements security technical measures and security management measures, and jointly builds a comprehensive and effective information security system。
Security programme design
Security technology programme design
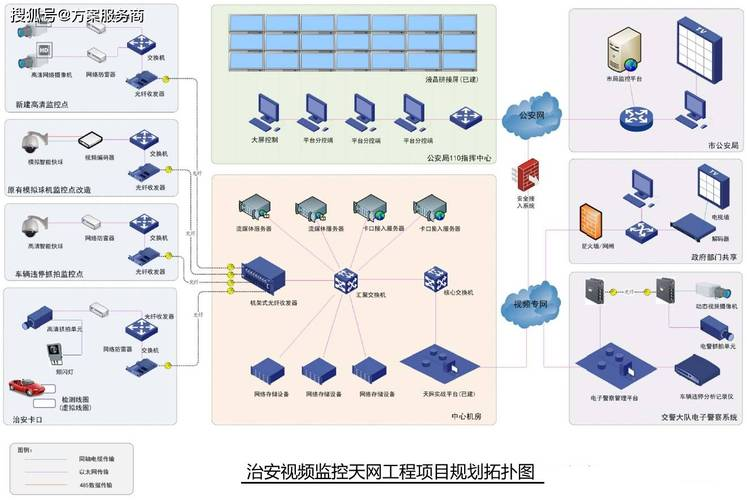
According to the concept of “vertical layers, horizontal subdivisions”, integrated surveillance systems can be divided into the following structures。
Figure 1 operational structure of the integrated monitoring system figure
The vertical side is divided into three tiers, the top being the central control centre, the middle being the station control layer and the lower being the field equipment layer. The workstations on the control level can control the distribution of equipment on the equipment level, but the number of workstations on the control level is large and, theoretically, any workstation can control the entire line of equipment. It is therefore necessary to treat all workstations separately, for example: only the general transfer workstation at the central control centre can control the whole line of equipment, the station workstations can control only the equipment at the station and the station's equipment can be controlled only by the station and the central control centre。
Since integrated surveillance systems are required to monitor multiple internal systems, such as the environment, fire and electricity, there is also a need to monitor signals, data from other professions, such as afc, cctv and pis, which are linked to these systems at the horizontal level. There is therefore also a need for zoning management of these internal and external systems and for segregation measures to prevent all losses。
In accordance with the principle of “border control, internal monitoring”, links to external systems (other professions such as signals, afc, cctv and pis) belong to the border and should be subject to access control. Internal systems, such as the environment, fire and safety doors, are monitored and the electrical system and the ring control system are on-site layers of equipment for the integrated control system, should be isolated and accessible. The training system is not directly linked to the operation of production and should be isolated by a network of independent groups, with access controls if there is a genuine need to connect to the production network。
As the security system is also deployed to stations, parking lots and vehicle segments, there is also a need for the security management centre to centrally and centrally manage the network-wide security equipment, and it is proposed that the security system be divided into separate management corridors in the communications system to reduce the impact on the production system。
The technical protection programme is designed in six areas, namely border protection, intrusion detection, security audit, mainframe protection, integrated security management and periodic security inspections, in conjunction with the extended structure of the integrated surveillance system, as required by the level of protection。
Border protection
Vertically, deploy firewalls between the control and on-site equipment layers of the integrated surveillance system, control bottom access of the integrated monitoring system workstation to the on-site equipment of the electrical system and the ring system, and prevent illegal access to the on-site equipment by bypassing the authorized control of the application layer。
Horizontally, deploy firewalls at the network borders of the integrated monitoring system and the interconnected system, protect the network and interface equipment of the integrated monitoring system from unlawful cyberattacks。
Invasion detection
Local area networks are monitored through the deployment of intrusion detection systems in central control centres, stations, vehicle sections and parking lots, and network intrusions, virus worms and ultra vires access are tested. Network behaviour is analysed for intrusion and alerts security management centres。
Security audit
The network audit system is deployed to the central control centre, the station, the vehicle segment and the garage, the application security audit of network access to the central database, the network audit of local area network access at the central level and at the station level, and the audit records are centralized in the security management centre。
Centralized certification, delegation of authority and audit of transport operations are carried out through the deployment of the transport security gateway at the security management centre。
Deployment of a log audit system in the security management centre to centralize the centralised storage of network equipment, security equipment, servers and workstation security logs。
Host protection
Installation of mainframe security protection software on ims servers and workstations and system-level protection of the mainframe, including security patch distribution, security baseline management, external storage control, network outreach control and virus protection。
The full-line security protection software is centrally managed by the security management centre, which sets up a unified security protection strategy, centrally distributes patches and viruses and keeps the ims mainframe in the best security condition。
Integrated security management
The establishment of a security management centre, the deployment of a situational awareness system and a security management station, which concentrates on centralized and unified monitoring of network assets such as network equipment, security equipment, servers and workstations, from the point of view of network security, and on the perception and presentation of the security posture of the network。
Centralize the maintenance and analysis of network security logs and centralize the management of security strategies, viral repositories and patches。
Regular security checks
Deployment of a security screening tool at the security management centre — the gap scanning system and the configuration of the verification system — to conduct a gap scanning and security configuration baseline verification of the network assets of the integrated control system, timely detection of network security issues and follow-up management and continuous refinement of network security protection measures。
The following is a map of cybersecurity protection in conjunction with the above six areas:
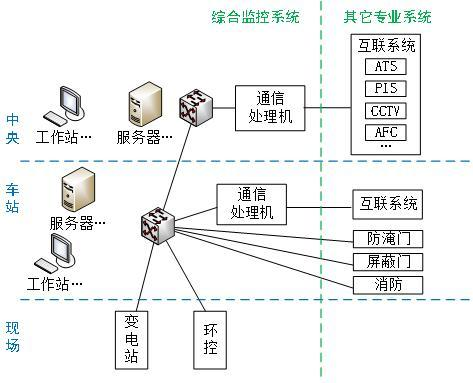
Figure 2 ims network security architecture
Security management programme design
Security management system
The most active factor in information security is people. The security management system described here includes the overall direction, strategy and management system that regulates the various security management activities, as well as the operational protocols for the day-to-day operations of managers or operators。
The security management system consists primarily of management systems, development and issuance, evaluation and revision. A system of information security management systems is required, and the development of regulatory regime requirements and the process of dissemination are further stringent and regulated。
Security management agency
The security management bodies include, inter alia, job placement, staffing, delegation and approval, communication and cooperation, and vetting and inspection. The placement of posts requires not only the establishment of a functional information security unit, but also a certain level of leadership at the upper levels of the institution, which has overall responsibility for the overall information security of the institution. The delegation of authority approval process controls were strengthened, as well as a phased review. Communication and cooperation were strengthened with external organizations and security advisers were hired。
Personnel security management
The management of personnel security is primarily related to two aspects: internal security management and external security management. These include recruitment, staff departures, staff appraisals, security awareness education and training and external access management. Increased recruitment, release and appraisal requirements for key positions, more targeted training of personnel and more specific requirements for external visits。
System construction management
Systems construction management is considered in terms of pre-engineering, construction processes and completed delivery, including system classification, security programme design, procurement and use of products, self-software development, outsourcing software development, engineering implementation, test collection, system delivery, system filing, grade assessment and selection of security service providers. The activities of the construction process require institutionalized regulation and implementation in accordance with institutional requirements。
System operations management
Management of day-to-day maintenance of information systems in accordance with basic requirements, using management systems and security management centres, including environmental management, asset management, media management, equipment management, network security management, system security management, malicious code protection management and password management. Keeping the system in the state of safety required for level protection。
Concluding remarks
The programme undertook a construction programme design for an integrated control system that meets the level of protection (level ii), both technical design and security management. The technical programme designed a security protection system based on an integrated surveillance system, based on the requirements of level protection (level ii), and carried out a reasonable security deployment design for the control centre in terms of network border security, network communications security and integrated security transportation, providing practical safety protection product deployment advice. At the same time, advice and advice were given on the information security management system。
The integrated urban orbital traffic control system, which guarantees the proper functioning of the subway, plays an important role in ensuring the safety of trains, passengers and staff, thus contributing to the improvement of the quality of orbital traffic and the efficiency of integrated operations. The present paper provides a comprehensive survey and detailed analysis of the safety of the network of the integrated subway control system (imms) in accordance with the level of protection requirements, in conjunction with the operational system, and proposes an information security system that meets both operational and level ii protection requirements。