Vehicle maintenance company network security optimization approach
Chapter i general provisions
The first is to strengthen the safety and security capabilities of the company's network, protect customer information, company core data and operating systems, maintain normal business order, improve the quality of services and customer trust, and promote the healthy and sustainable development of automobiles, and to develop this approach in conjunction with companies in accordance with laws and regulations such as the law of the people's republic of china on cyber security and the law on data security。
This second approach applies to all sections of the company, all employees and all equipment, systems, including but not limited to customer information management systems, maintenance of data platforms, office automation systems, networked maintenance diagnostic equipment, employee terminals, etc。
The third category of corporate cybersecurity is based on the principles of “preventive ownership, prevention combinations, responsibility and full participation”, integrating cybersecurity into all aspects of day-to-day operations, building a technical and regulatory security protection system, and establishing digital barriers for high-quality company development。
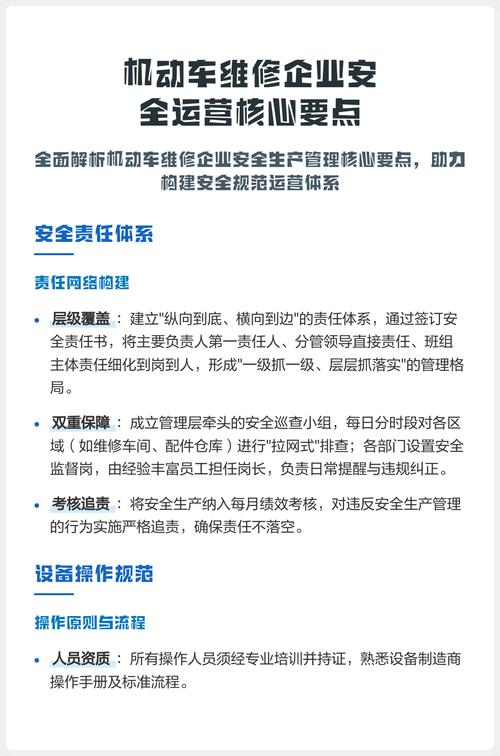
Chapter ii organizational structure and division of responsibilities
Article iv establishes a steering group for cyber security, headed by the general manager and headed by the deputy general manager for administration and technology, comprising the heads of the departments of administration, it, client services and maintenance technology. The leadership team is responsible for integrating security planning, critical decision-making and emergency response, ensuring network security and operational development are deployed and advanced。
Article v it is the day-to-day management department, with specific responsibilities including: integrated technical protection system construction and maintenance, periodic security testing assessments, staff training, handling and reporting of safety incidents, and technical implementation rules。
The heads of the article 6 departments are the first to be responsible for security in their department, and are required to ensure that employees comply with the regulations, implement measures and report security risks in a timely manner; all employees are responsible for the security of terminals and accounts they use and are conscious of the need to maintain network security。
Chapter iii technical protection system optimization
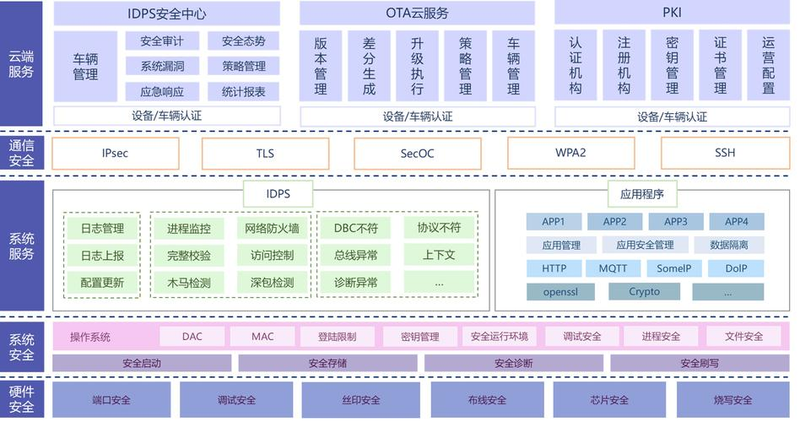
Article vii network architecture upgrades: implementation of office network, operational system network, maintenance equipment network logical isolation to limit cross-area access; deployment of firewalls, intrusion detection and defence systems to monitor traffic in real time; optimization of wireless network security, use of wpa3 encryption and prohibition of private networking。
Article 8 data encryption and backup: customer information, maintenance of core data transfer storage using aes-256 encryption; establishment of daily incremental, weekly full backup mechanism, backup data being stored off site and regularly restored for testing; waste media physical destruction or professional removal。
Article 9 terminal protection enhancements: employee terminals need to be equipped with regular poison-killing software and firewalls to open automatic updates; the installation of unauthorized software and access to unknown equipment is prohibited; complex passwords are created and replaced every 90 days, with no automatic 10-minute lock screens。
Article x: detailed access controls: minimum authority by post, double-factor authentication of the operational system; logs of access to the records system, kept for not less than six months。
Chapter iv, data security specialized management
Article xi protection of customer information: collection of information in accordance with the “lowest necessary” principle, for business purposes only; prohibition of disclosure of customer information except with consent; periodic audit of customer information systems to screen unusual operations。
Article 12 maintenance of data management: maintenance records, breakdown of failure reports with sensitive levels and level protection; networked diagnostic interfaces with authority to prohibit unauthorized operations; core data prohibit private reproduction。
Chapter 5 staff safety awareness promotion
Article 13 normalization of training: quarterly security training covering regulations, fishing techniques, data protection, etc.; entry of new staff on duty requiring a specific training examination to qualify for induction; annual invitations