The cloaking law
The cloaking method refers to two different versions of a web page, one for the search engine and the other for users. It was a serious deception of the search engine to cover up the real content of the web page like a cape, especially in the grey industry。
9. Phytotechnologies
A parasite is an intrusion into another's website and the implantation of a parasite program and the automatic generation of illegal pages, which leads to the flow and delivery weight of the target website. And it's called a parasite because it breeds indefinitely, without the need for intervention. It's terrible
10. Mirror technology (web image)
Mirror technology generally refers to mirror sites, other sites that are essentially the same as your site and are synchronized in real time, like mirrors, so it's called mirrors. Mirror sites can be negative to seo your site, use your content to get a higher ranking and then turn users to sensitive, illegal content sites。
11, spider hijacking
Spider hijacking is the hijacking by seoer of the search engine spider (e. G. 100 degrees spider, google spider) by various irregular means, as shown by the fact that the 100 degrees snapshot is a page and the user clicks on the site to see another page. This is usually done according to the user-agent of the visitor. The technical rationale for spider hijacking is to hack into the hunting site and upload a document (scanning the file, looking at the search engine) in one of the folders or root directories to reach the hijacking site and to the target site. It is well known that a large part of the web traffic comes from spiders, who hijack the search engine spiders and the search engine flows into the target site。
Solutions to the problem of spider hijacking
If we find out there's a problem with spider hijacking on our website, the first time we check if there's a carousel file in our website space, and it's usually a global. Asa, the name of the file will be renamed at this point, and this horse program will not be controlled at this time, because we can't delete it, and only space operators have the right to delete it. After renaming the horse file, the spaceman helped to delete it。
12. Pr hijacking technology
Pr's method of hijacking is to use jumps. Pr hijacking techniques typically include the law on kidnapping by domain name, the law on transmitting domain names, the law on transmitting kidnapping by domain, the law on transmitting kidnapping by name, the law on transmitting kidnapping by name, the law on transmitting kidnapping by name, the law on transmitting kidnapping by name, the law on transferring kidnapping by name, the law on transferring kidnapping by name, the law on reporting by name, the law on kidnapping by name, the law on transferring kidnapping by name, the law on kidnapping by name, the law on reporting by name, the law on kidnapping by name, the law on kidnapping by name, the law on transfer by name by name, and the law on kidnapping by name, the law on transfer by name, the law on kidnapping by name, the law on transfer by name, the law on kidnapping by name, the law on transfer by name, the law on transfer by name, the law on transfer by name, and the law on hijacking by name, the law on hijacking by name, the law, and the law onRame hijacking the pr act, masking the bell hijacking the pr act. Through pr hijacking techniques, the website can quickly reach a high pr value to achieve a higher ranking。
Pr hijacking inspection methods
(1) using official pr testing sites。
(2) it is very suspicious to see google's pageshots, google's snapshots and the web pages that you see are not the same website (both generic web titles and logo will be shown), which is the website of the ppr hijacking target. The shortcomings of the method: as long as the website is updated to its own site after the hijacking, google re-enrolles the new site, and at this point no trace of the original site can be identified, and it is impossible to confirm whether the pr hijacked the site, much less which one was hijacked. This method only applies to the immediate conversion of the target site to its own site。
(3) view the reverse link and then judge which site is the real one according to the reverse link。
Trash links
Linking refers to links in large forums and blogs that are not relevant to content and automatically generated (collected) pages, known as spam links, to achieve rapid keyword ranking. Many seoers have previously done more or less so, and all search engines have identified the outer chain as one of the main factors in their ranking, and obtaining natural links from other sites is not so easy, so the garbage link has been created。
The garbage link will not be immediately identified, but will be reviewed ex post and its weight removed, leading to a reduction in power. The trash link is included in the keyword ranking weight before it is recognized. The impact of this type of garbage link on the search engine is now severe, and the scrutiny of the various loading platforms is being strengthened. Even if only temporarily adopted, subsequent detection by a search engine or website manager would result in a larger external chain swing on the site, a black hat seo technique that is as useless and easily discovered as a stack of keywords。
14. Purchase of links
Even though the green diamond algorithm 2. 0 has been emphasizing the risk of purchasing links, there are still a number of websites that buy links to increase weight. Now that a 100-degree circumvention algorithm has been put in place for the link, we can be sure that the link can affect the ranking and be identified。
If the website is considered to be cheating through the purchase of links, there is no way to argue with the search engine, which is the final decision. But it is difficult for the search engine to judge which links are normal and which are purchased, which is why it is known that the counterparty is buying the links and that his ranking has always been higher than yours. It can be said that many of the websites that are now ranked above have links, so long as they are "regular" and have reasonable access, there is nothing to worry about. All that needs to be feared is those websites that trade in web links, because search engines can find them。
Indexing
This self-absorption is a technique that can only be done by a new station chief and is not a black hat. In fact, the index is used to increase the weight of the website, and the estimated weight of the station master tool is more of the flow estimated by the 100 degree index. The index could increase weight, but it would be of little benefit。
16, 100% share
Through the 100% sharing button, your web page will be more easily discovered by the 100% search engine, which will give you the opportunity to bring back more traffic from the 100% search. A hundred thumbs can be found in the search results, and even if the ranking is not first, it will guide users to your website。
It's an official statement that has been shared:
(1) users share their content on third-party websites, and users of third-party websites click on their own shared links, bringing socialized traffic from third-party websites。
(2) a 100-degree shared web page can be detected faster by the 100-degree reptiles, thus helping the content of the site to be faster。
(3) once the 100-degree shared web page is shared by the users, the number of times the page is shared is displayed in the 100-degree search result page, which helps users judge the quality of the web page。
The search engine's own operating guidelines were a constant improvement in the quality of seos, providing more valuable information for visitors and it hoped that all sites would follow its established rules of the game. This sharing tool, which is the largest search engine in the country, was originally designed to provide them with a more valuable search result. We assume that it has some effect on our ranking, and you use a brush to provide this value, which is tantamount to buying a link, and if you do so at your site, you may face the penalty of a search engine。
17, brushing web traffic
Often, website traffic refers to the number of visits to a website, which is used to describe the number of users accessing a website and the number of pages viewed by users. The commonly used statistical indicators include the number of independent users of the website, the total number of users (including repeat visitors), the number of page views, the number of page views per user, the average time spent by users on the site, etc。
Harnessing website traffic on website ranking
(1) suspects of fraudulent high-volume flows
Since the flow of platform brushes is very fast, with tens of thousands of ips per day, hundreds of sites are already very good every day, and a new station has suddenly increased from less than 10 a day to tens of thousands a day。
(2) repeated ips are of serious interest
Because of the thousands of users of the same platform, there is a long-term repetition of the ip, which can easily draw the attention of the search engine and alexa。
(3) short page views
Because of the software platform, the software is closed as soon as it opens the page, otherwise the browser cannot afford to open too many pages at the same time. The page viewing time is short, and even if it is really natural for the internet to browse, a website is too short to prove from one side that it is not readable, that users experience poorly and cannot keep their customers。
(4) uneven flows
In particular, for a new website, there was no traffic at the beginning, with almost zero ip visits per day. When you turn on the flow of software, the number of ip accesses has increased instantaneously to dozens, hundreds or even tens of thousands, and serious ip access is uneven, and it makes sense to be demoted by search engines and alexa。
(5), serious imbalances in external chains and flows
As a rule, a new site flows thousands or even tens of thousands of times with few high-quality external chains, and even one of its masters cannot do it, not to mention a new root station chief. A professional team like the search engine and lexa are even more demented. Of course, that's the extreme. There is a certain advantage to the ranking of a website if it is a reasonable flow of brushing, but it is simply for the sake of seo and seo, and the traffic generated by the site is all false, but when you are ranked, it is also possible to obtain more effective traffic, which is the same as buying links。
18. Spider pool
Spider-pools are used primarily to complement the program that leads to the cobweb trap of the seo search engine, like the biduspider, and we all know that the process of ranking the website is the search engine spider capture >web capture >to create index > web keyword ranking, a process in which the significance of the spider-pool here comes out, by cobing spiders, by leading spiders to get lost in your program, by keeping web pages accessible and facilitating the rapid ranking of the black hat seo。
Iii. The danger of the black hat seo
1. Impacting brand image
The black hat seo website optimizes the use of keywords, out-chains, etc., and while the ranking of the site's search engine can be raised in the short term, this short-term website ranking will soon fall off, as well as creating a bad impression of the brand。
2. Impact on user experience
Many of the black hat seo technologies operate against user experience, and the use of black hat seo technologies leads to a vicious cycle, leading to poor user experience and leading to large fluctuations in the ranking of search engines。
3. Deprivation of the website
Once identified by the search engine algorithm, the black hat seo may lead to punishment and downgrading of the website, which, once k, takes a long time to return to normal ranking。
4. Low success of black hat seo
The success rate of the black hat seo technology is also low, with a 30% success rate, which is good. If you have the time to invest, it would be better to do well with the white hat seo technology。
5. Short life cycle of black hat seo technology
The black hat seo has a very short life cycle, and even if the search engine is temporarily ranked, the search engine's seo rules are constantly updated and the loophole cannot remain. It is important that the seo be focused on user experience, and that the optimization of the search engine, which does not focus on user experience, is destined to flourish。
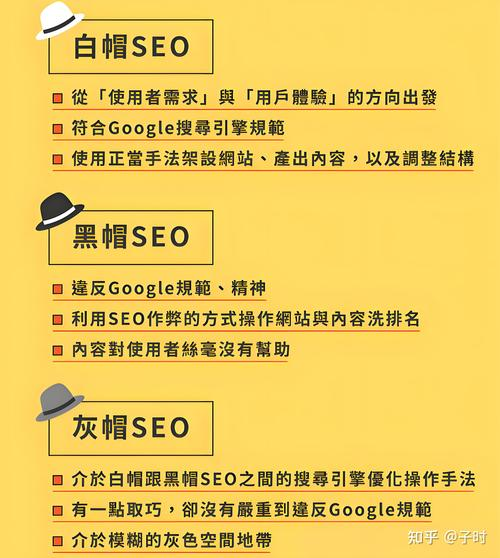
Iv. Distinction between black hat seo and white hat seo
Black hat seo is different from white hat seo's long-line fishing strategy. The black hat seo is more focused on short-term interests, which are driven by a large amount of profit through cheating. The black hat seo mainly includes the optimization of the website in a series of ways that violate search engine rules, such as keyword stacking, portals, hidden text, malicious re-direction, etc., affecting the legitimacy and fairness of the search engine's ranking on the site. The main objective of the black hat seo is to rapidly raise rankings in order to gain more traffic and profits, but this approach can have a negative impact on user experience and can be penalized and blocked by search engines, thus losing user confidence。
♪ white dimensional hat ♪
Core objectives

Provide long-term quality content and enhance user experience
Short-term quick ranking, ignoring user experience
Optimizing tools
Means of compliance (original content, natural outer chain, etc.)
Cheating techniques (keyword stacking, hiding text, buying external chains, etc.)
Sustainability of effects
The rankings are stable, long-term
Ranking may increase in the short term, but can be easily penalized by search engines (e. G. Power of reduction, shielding)
Risk
Almost risk-free, industry-compliant
High risk of websites being penalized by search engines
The white hat seo refers to an optimised approach to complying with the principles and norms of the search engine, which includes, inter alia, a range of actions such as content optimization, website structure optimization, inner chain construction and external chain construction. The main objective of the white hat seo is to improve the user experience of the website and the ranking of search engines, thereby increasing traffic and conversion rates. The white hat seo follows the "user-centred" principle and respects the search engine rules, thereby gaining the trust of both the search engine and the user. The white hat seo is concerned with long-term benefits, which take a long time but have a steady effect。
Summary
Optimization of the 猩seo: the black hat seo is a technical tool for violating the law, not using black hat seo technology to raise the ranking of the website. The black hat seo is also at high risk, and the search engine finds itself at risk of being exposed to k-stations at any time。
References:
Black hat, seo
Https://baike. Baidu. Com/item/%e9%bb %91%e5%b8%bdseo/6111825
What's black hat seo? Black hat seo technology inventory-csdn blog
Https://blog. Csdn. Net/weixin 4372177/article/data/123609059




