Precaution, deception
To strengthen self-defense




Knowledge campaigns to prevent fraud in telecommunications networks


Prevention of telecommunications fraud

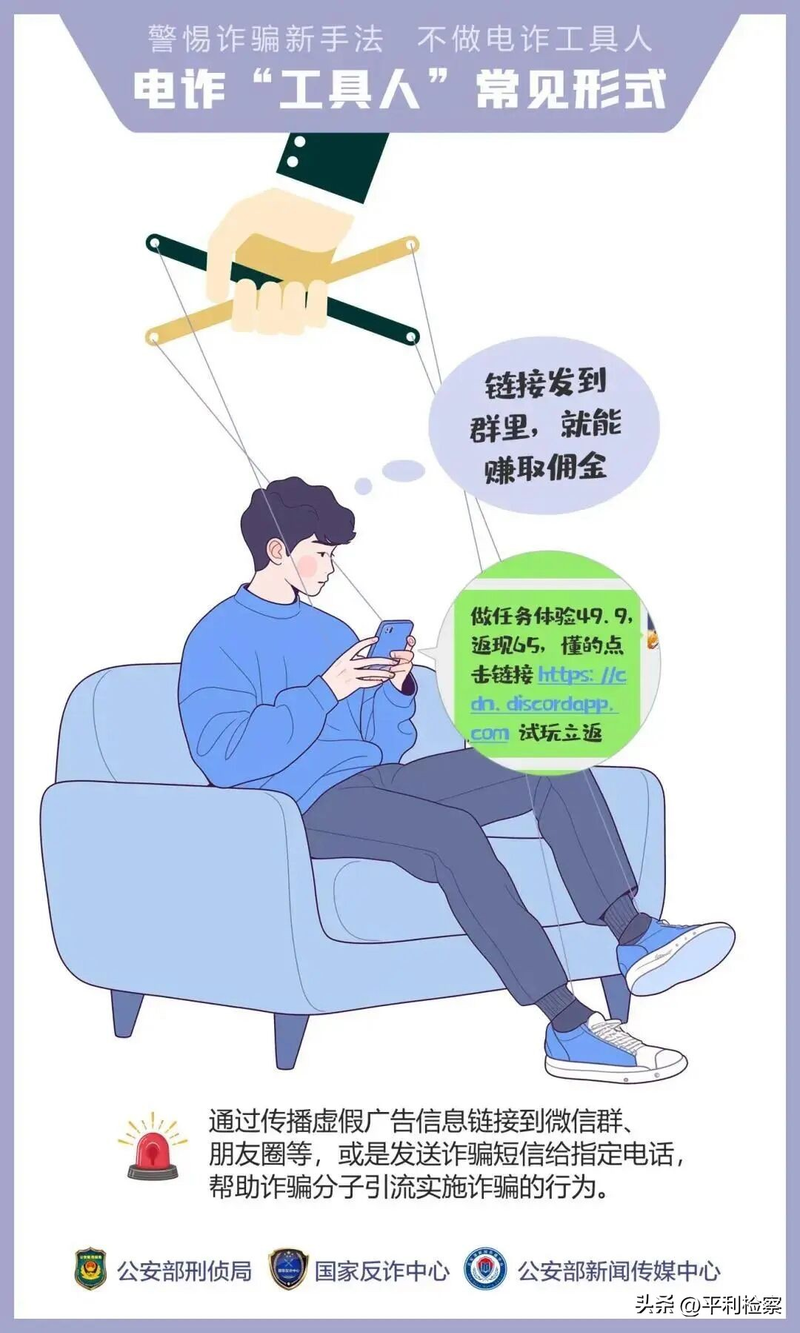
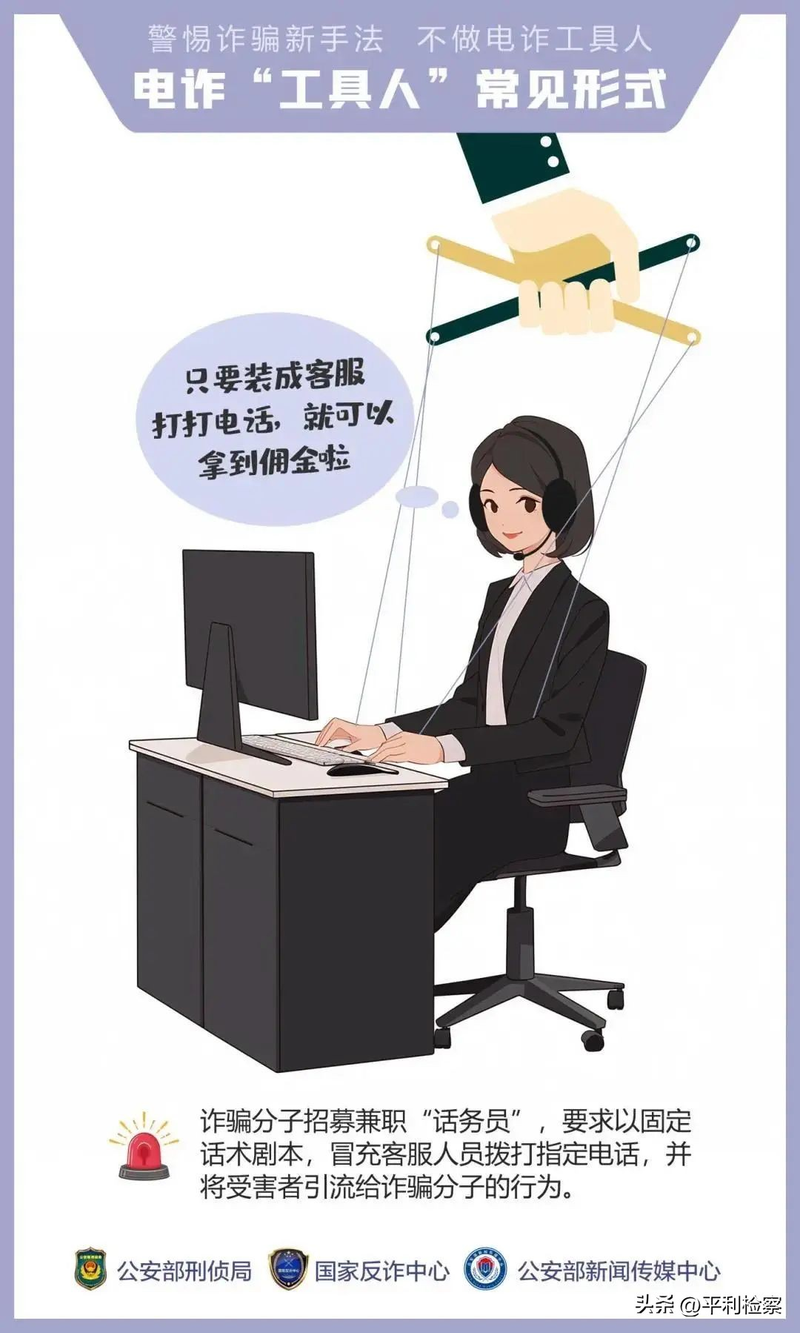
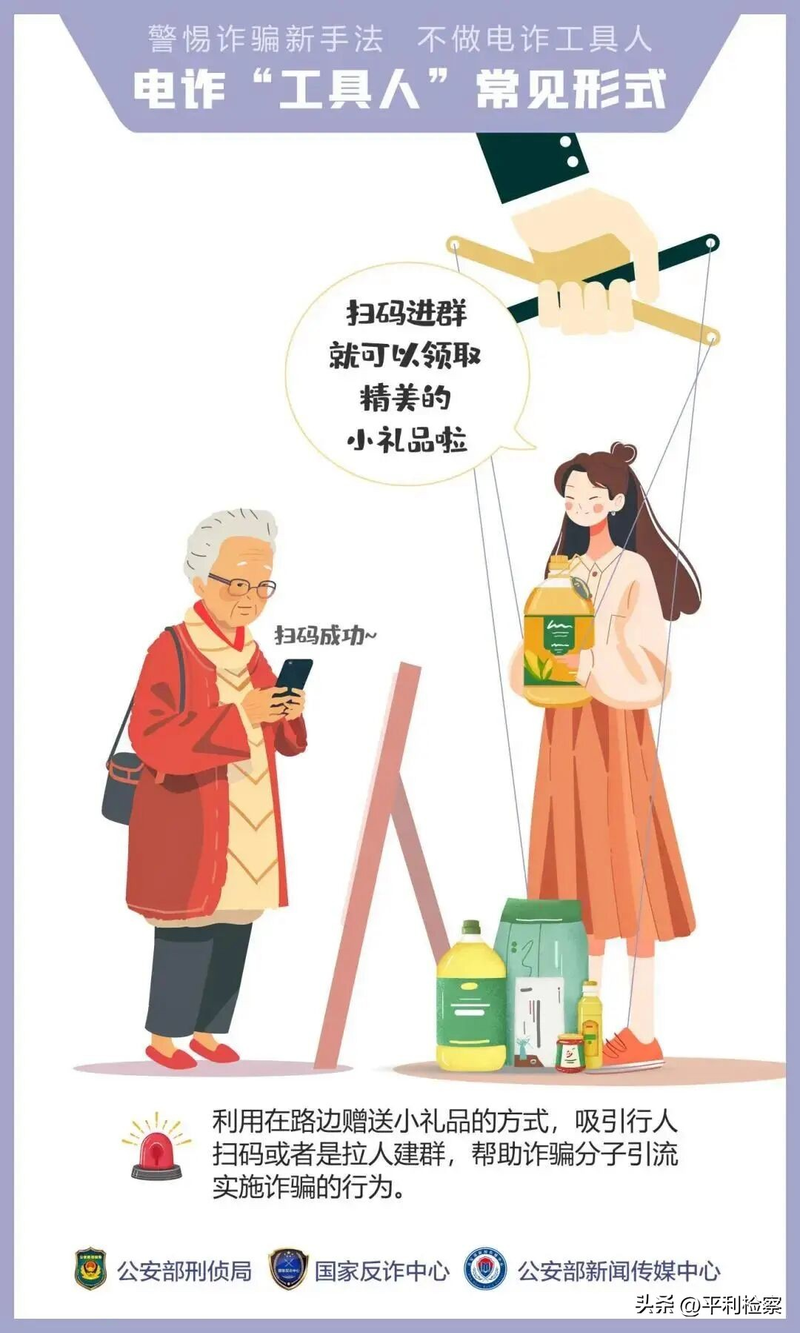
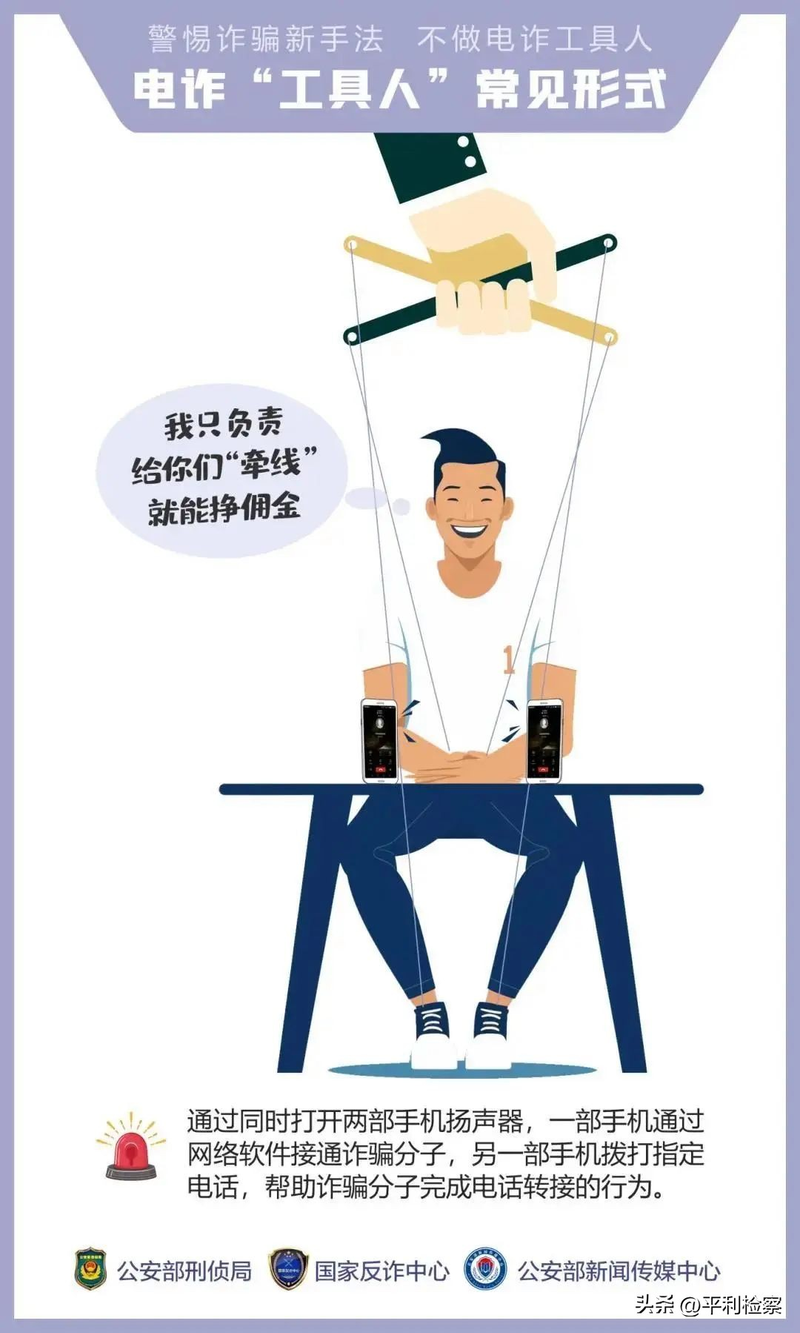
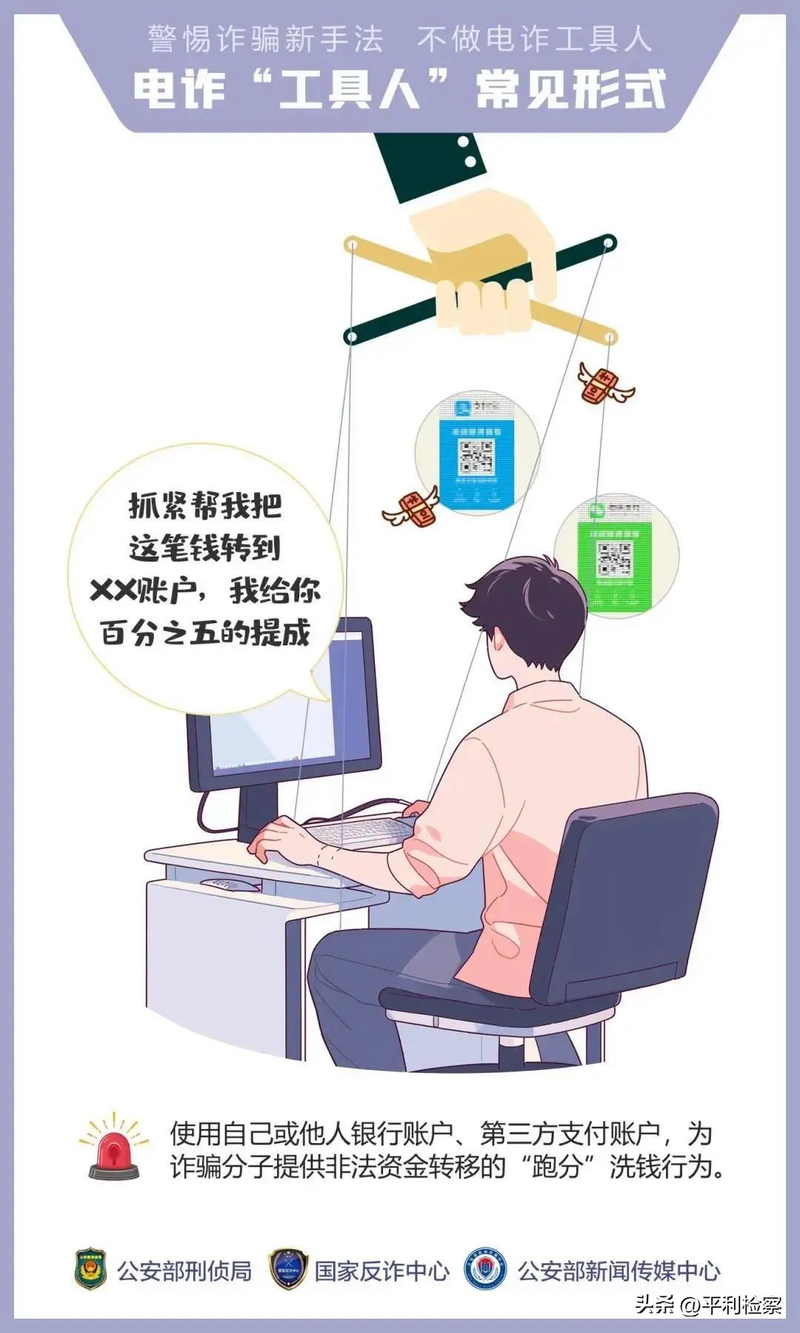
In recent years, telecommunications fraud has increased with the rapid development of information technology and the spread of the internet, posing a serious threat to the property security of people. How can we be wary of the “dumping” trap and avoid becoming “toolmen” of fraud? Let's go into today's common law class and learn a few common forms of telecommunications fraud。
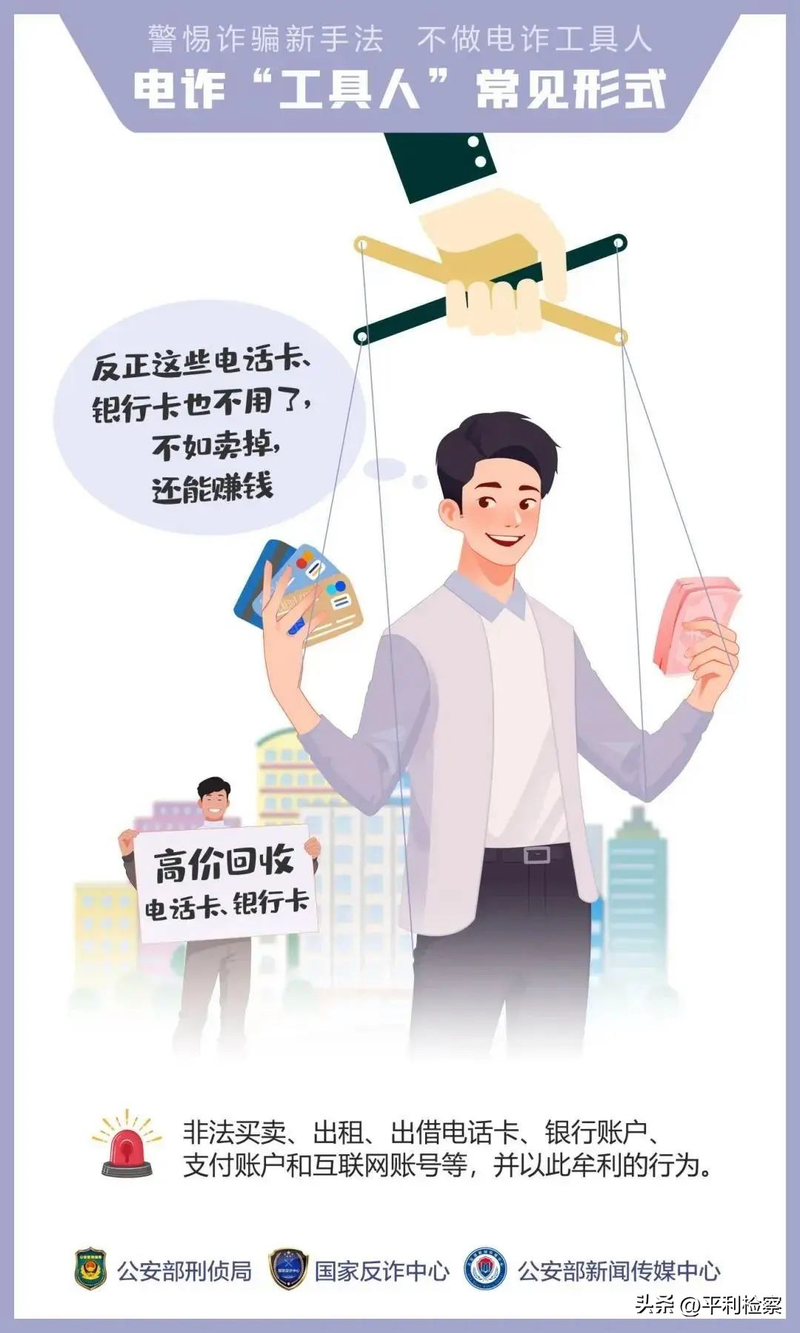
I. Leasing and lending bank cards
Ii. Money-laundering in part-time procurement

Iii. Money-laundering in cash

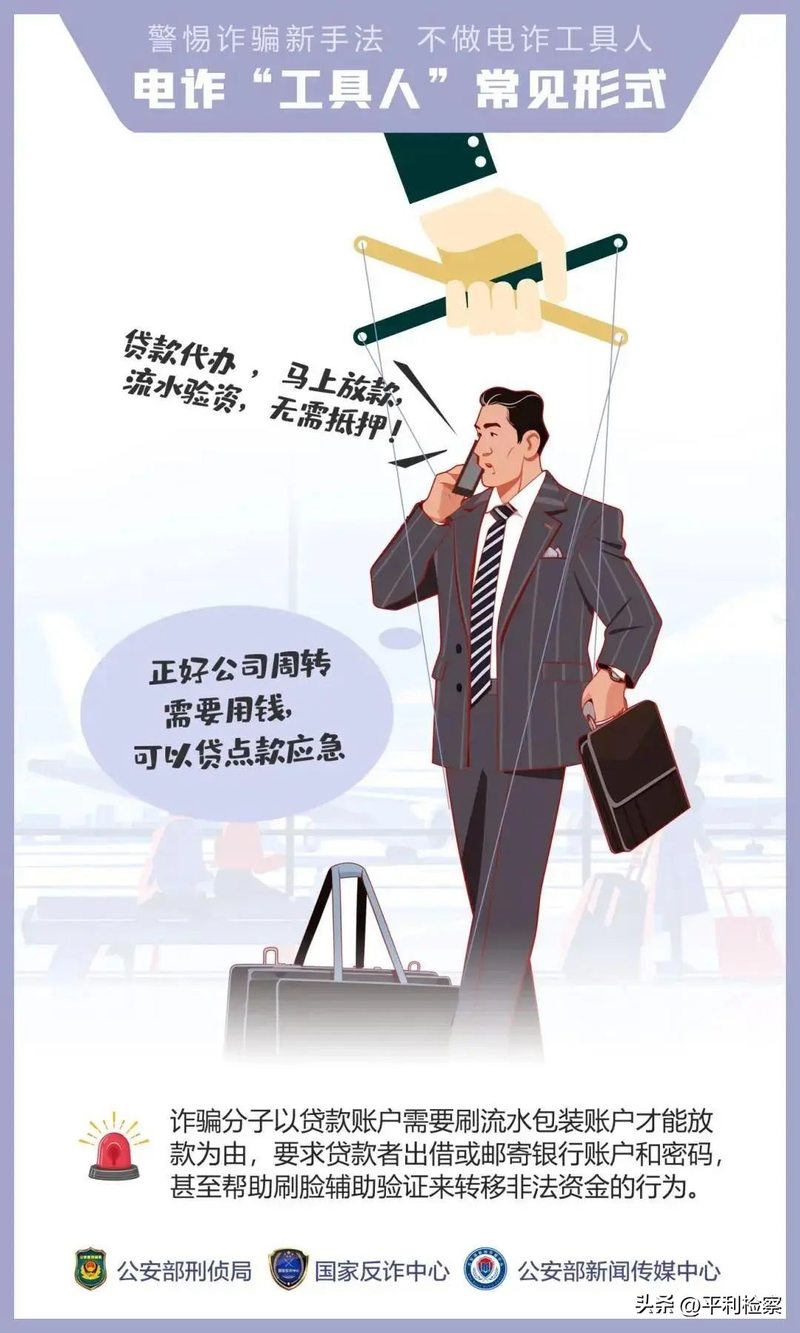
Iv. Money-laundering of loan brushes
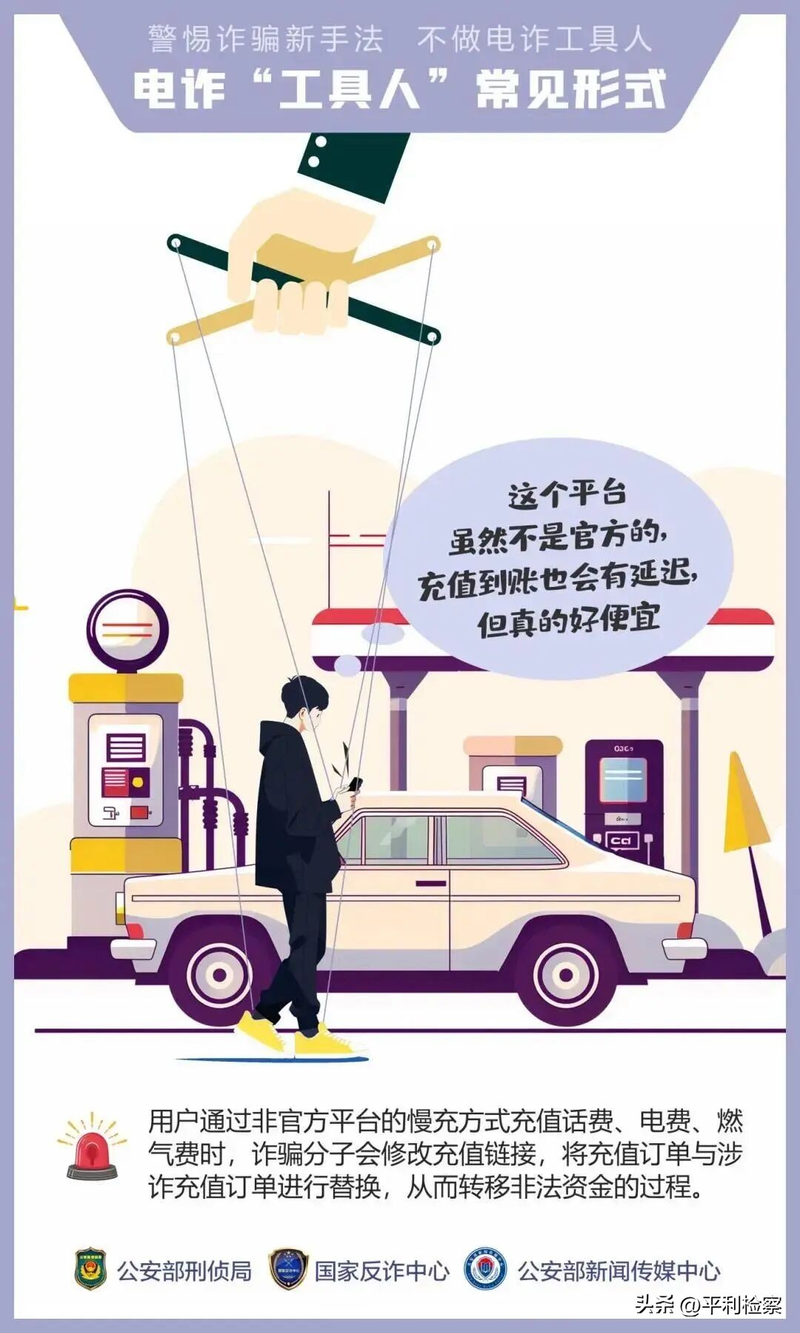
V. Calling, equipment, corrective gas
Vi. Receiving poverty poverty responsibility monitoring

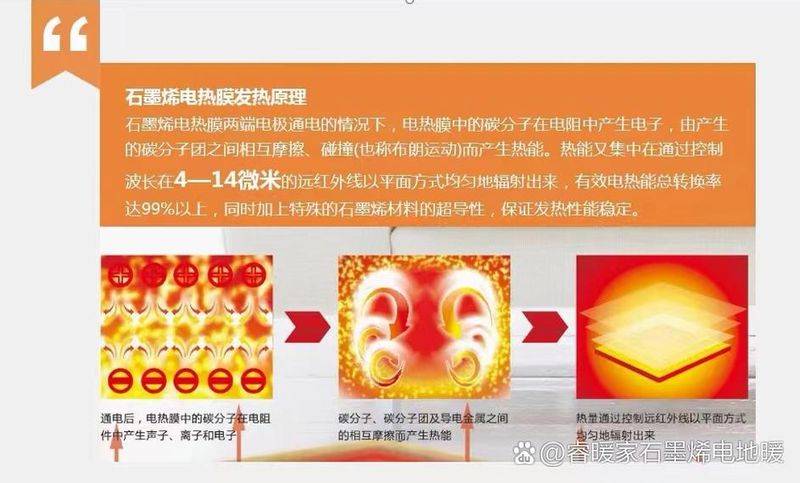
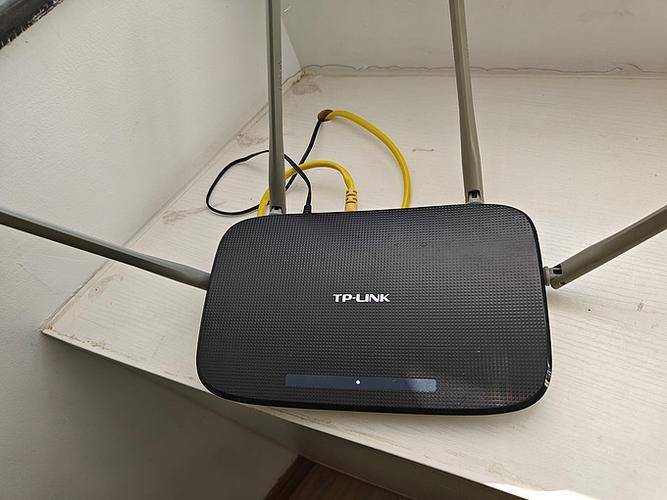
Vii. Using goip, voip to operate a scam, “helps build a device to collect a commission”

“scrutinizing” “scanning presents”? It's actually a front-end for fraud

Ix. Part-time collection of money for illegal molecules

X. What are the ways in which electro-frauders lure people into becoming “toolmen”
Anti-fraud little knowledge
The form of fraud is constantly evolving and is becoming more disguised, with the population suffering economic losses with little care. In order to protect the legitimate rights and interests of the population at large, to strengthen anti-fraud awareness and to enhance its capacity to do so, the financial consumers' protection service of the general directorate of financial supervision draws the attention of the public to the following four points。
No blindness, no trust, no petty fraud prevention
To build a scientificly rational concept of investment finance, to raise risk-prevention awareness and information screening skills, and to be vigilant about the rhetoric of “tips falling out of the sky” such as refunds, gifts, high rates of security, high prices for purchases, etc., so as to avoid the risk of being cheap and cheap. To avoid blindness or opportunism, to believe in “broadcasts” where there is no clear way of doing so, and to believe in “stable profits” or “high profits”. In selecting items for disposal, formal financial institutions should be selected and the terms of the contract carefully read, their risk tolerance should be fully assessed, products tailored to their needs should be selected, fraud detection and fraud prevention should be enhanced and property damage should be protected。
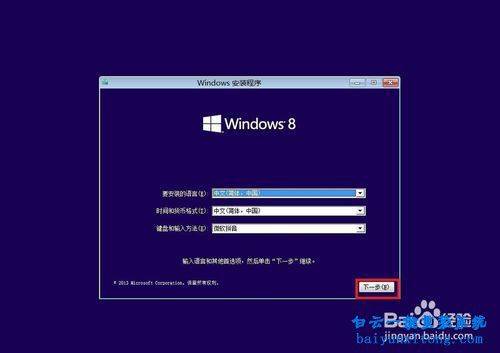
Reject shared screens to protect information from leakage
To raise awareness of the protection of personal information and to secure information such as id numbers, bank cards, account passwords, authentication codes, personal biometrics, etc. Not randomly click on uncharted links, not randomly download strange software, register strange platforms or add strangers, be vigilant about the security of personal social accounts, reject strangers' “shared screens” requirements, avoid unconnected manipulation of electronic devices such as their own mobile phones, computers, etc., and avoid financial loss due to the disclosure of personal information. At the same time, protection measures for personal information should be strengthened, account security set-ups should be regularly checked and anomalies detected and addressed in a timely manner。
Money transfers are strictly closed
There is a need to be vigilant when it comes to transfers and money transfer operations, and to guard against the risk of fraud. When receiving telephone calls, text messages or web-based information relating to requests for transfers, the authenticity of the information is verified in a timely manner through official agencies, the transfer requirements or inducements of a stranger are not trusted, the account numbers provided to a stranger are not transferred, and the transfer of funds to unrelated accounts is not made at will. Careful verification of each other's identity and information is essential before transfers are made, ensuring that funds are transferred to truly trustworthy persons or institutions。
Regular channels to protect their interests
In the case of economic disputes, the rights are protected by law through formal channels, such as mediation through a third-party mediation organization or recourse to the judiciary. If it is discovered that it has been caught in a fraud trap that has led to the destruction of funds or that leads to a suspected criminal offence, the relevant evidence, such as chat records, audio recordings of telephone calls and a screen check of transactions, should be kept and promptly communicated to the public security authorities. At the same time, organizations or persons on the internet that claim to be “wilders” cannot be trusted to avoid being deceived again。