The closed-door system is a more user-friendly security system for modern commercial buildings, neighbourhoods, schools, businesses, etc. The closed-door system is the first to wash a modern security management system that integrates the technology of automatic micro-recognition and modern security management measures. Door-ban systems are used more in our life work, but what do you know about their installation? The following sub-editorials provide an opportunity to share information on the installation and failure removal of the closed system。
Installation i: device installation
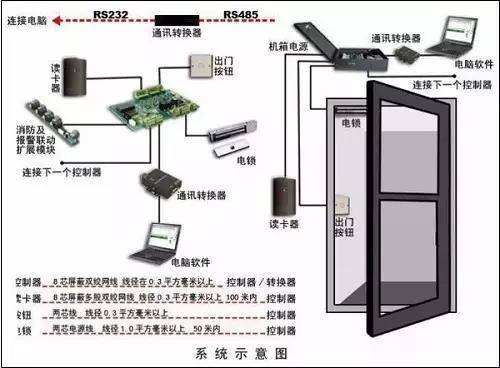
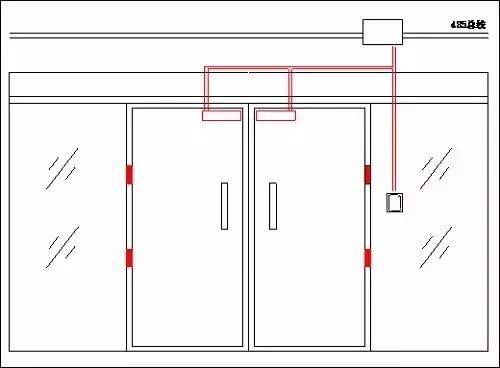
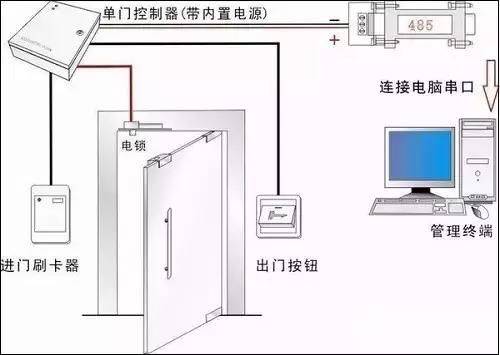
1. Front end equipment
A. Installation of card readers at entry points. In the case of card readers, do not approach or contact high frequency or strong magnetic field (e. G., heavy motors, monitors, etc.) and are required to cooperate with the location of the control box。
B. Installation of exit buttons。
C. The electromagnetic locks are mounted on the top of the door and the door frame。
D. To ensure safety and beauty, controllers and power tanks may be installed on site or in weak wells. The advantage of on-site installation of controllers is to save on the use of wires, which are installed in weak wells to facilitate the future maintenance of the system and the security of the system, as well as to place controller boxes above card readers near the electromagnetic locks. The manner of installation may be selected according to the client。
2. Central control equipment
A. Control mainframes and keyboards are installed on a wall or on a workstation。
B. The alarm device is placed in a better location。
C. Due to the special nature of the closed system, which requires good power supply to the system, it is recommended that a ups power supply be used to centralize the closed system。
Installation ii: debugging equipment
Upon completion of the installation of the system, the pass-ban card signal is entered into the mainframe and the pass-ban card is detected separately, with any omissions or misstatements. This route is cleared for access to the other route, so that each route is individually tested and all routes are reconnected once confirmed。
Managers may delegate authority on the basis of the authority to use persons, and if some persons have access to any place at any time, ordinary persons may only enter and leave the delegated authority within the time frame of the authorization on the basis of the authorization card. When all doors are regularly and illegally opened, check if the control centre computer has a record。
3. The attempt centre computer cannot be connected to the controller for failure or other reasons, whether the controller can record independently relevant information on the door point controlled, whether all information can be automatically uploaded when the centre computer is connected and whether the integrity of the information record can be guaranteed。
4. Debugging records。
5. Finalization of completion report。
Installation iii: pipe installation
1. The installation of the wiring shall conform to national regulations; the construction and inspection of electrical installations; and the relevant regulations and regulations issued by the state。
Pipelines in the tube or in the chute shall be performed after the building has been wiped and ground works have been completed。
Water and miscellaneous items should be removed from the tube or from the trough before crossing the line。
Lines of different systems, different levels of voltage, different types of current should not be worn in the same tube or in the same slot。
There should be no connection or twisting of the line inside the tube or the sink。
The link to the lead should be welded in the connector box or connected with a root。
The small cross-section system connection can be hanged, with a number above five strokes and then tinted with insulation belts。
The pipeline passes through the deformation of the building (including the sediment stitches, stretch stitches, anti-shock stitches, etc.) and should be compensated, and the steering line should be fixed across both sides of the deformation stitches, with an appropriate residual amount。
The end in the end of the trunk of the connection should select the endboard with the pressured or welded point, which should have a proper sign on the end of the link。
2. The door-ban controller shall be robust, unslanted and clearly marked。
Installation on light walls should be reinforced。
(b) cables or wires introducing door-ban controllers, which shall be aligned, avoid cross-cutting, and shall be marked by a fixed cable core line and the parts of the line assigned to it, and shall not fade easily with the drawings
(b) the end panel and each end of the line shall not exceed two
Cable cores and conduits should have more than 20 cm
Wires shall be bound into beams; when a lead leads through the line, they shall be blocked at the point of entry。
3. The main power source introduction line of the door-ban controller shall be directly connected to the power source, the power plugs shall be strictly prohibited and the main power source shall be clearly marked; the door-ban controller shall be secure and clearly marked。
4. Control the route and specifications of the interior terminals to conform to the design requirements. The construction shall be carried out in accordance with the following provisions:
(b) the surface of the main line should be complete, with no visible damage and residual welding sludge, and the copper belt beam light, with no giraffe, and the insulation layer should not be exposed to aging turtle cracks
The main line shall be laid in the centre of the sink or cable walkway and shall be fixed on the outside side of the sink, and shall be flat and shall not be tilted or bent。
The connection of the main line to the rack or roof should be strong
The copper belt matrix on the cable lanes can be fixed by screws, and the copper node on the cable lanes should be tied to a crossbar
The engineering and mine-protected installation of the system should be carried out strictly in accordance with the design requirements。
Local installation should be carried out in conjunction with civil construction。
Four exclusions from door-block failure
Methodology i. Software testing
1. Test method: start management software, access to the main console selected door, click on the detection controller, and the software operation information will indicate the associated malfunctions, which can then be processed on the basis of relevant information。
Real-time monitoring: general control - real-time monitoring, real-time monitoring of the corresponding swipe card indicator to facilitate detection of failure to open the swipe card。
Search. Net: basic settings - controllers - search. Net, which helps to detect communication failures in the tcp/ip controllers and facilitates the detection of communication failures. Attention: please close the firewall
Method ii. Hardware indicator light method
1. When electricity is turned over, we can see the power beacon power, the cpu signal flashing to determine whether the controller is working。
When you swipe a card, you can look at the card light and see if the read card data is transferred to the controller。
Press the out-of-house button, so we can see if the relay signal is ringing and determine if the controller relay output is normal。
4. Tx and rx lamps, tcp controller rx (l)Ink) lights are often lighted to signal the connection. Tx light flashing indicates communication。
5, err light flash represents a malfunction in the controller and details are obtained in the software tests。
6 the video controller can also view the power signal, and whether or not the rj45 signal blinks alternately at ping。
7,485 active converters are scintillated to determine whether the computer is capable of sending data。
Method iii. Replacement exclusion
1. Replacement of equipment: this is a point of reference, which cannot be fully established, because if an environmental or factor-induced situation does not necessarily appear immediately, as if a human chronic disease had a latency period, the same problem would arise after a period of time, and if the equipment that has been replaced is suspected of being problematic and is detected separately, which may be a problem of environmental disturbance such as wiring, the source of the failure should be actively pursued。
Computer replacement: it is possible to determine whether it is the computer of the customer or the operating system environment, the virus, the serial output or the setting is incorrect。
3 databases, software replacements: for example, failure to extract records or upload settings, failure to generate reports, etc., another completely new database or software can be used to determine the scope of the problem。
Method iv. Separation exclusion
With the door-ban controller at its core, many of the equipment charged can be picked up outside, while the quality parameters of the off-link equipment are uneven and may be interfered with, leading to a strange phenomenon, such as re-launching of the controller, err lights, abnormally open doors, separation of the additional equipment to see whether it is normal, and then loading each of the various outside equipment and loading a test to see what has caused the malfunction, such as the tribar, gate, electric bells, elevators, automatic doors, and various alarm devices outside the extended panel, which may be the source of interference。
2-485 means of communication, a system with 8 controllers, could consider cutting off the four in the back and then cutting down the search range by two of the remaining four, or cutting off the second and connecting the back to the line of communication, depending on which one is not working。
3. Tcp controllers use conventional methods that are not properly connected to the customer network and can test ok independently from the customer network using an independent switch, seeking acvm support to see if other network authentication restrictions are activated。