Introduction
As people's standard of living improves, the problem of how to achieve home-based piracy becomes particularly prominent. Traditional mechanical locks are favoured by a wide range of users because of their simple construction and frequent incidents of scavengers。
Two scenarios were conceived in the design of this topic: one for single machine control at the core of at89c2051; the other is the digital logical circuit control program, consisting of 74ls112 double jk triggers. The latter option is used in this paper in view of the complexity of the rationale for the single machine programme and the cumbersome debugging。
2 overall programme design
2. 1 design thinking
A total of nine user input keys were created, of which only four were valid password keys and the others were jamming keys, and if the jamming keys were pressed, the keyboard input circuit was automatically zero and the password originally entered was invalid and had to be re-entered; if the user enters the password for more than 40 seconds (in general, the user does not exceed 40 seconds, and if the user finds it difficult to do so, it can also be modified) the circuit will be alerted for 80 seconds, and if the circuit calls the alarm three times, the circuit will lock the keyboard for five minutes to prevent illegal operations by others。
2. 2 overall box charts
620)this. Width=620; "style="cursor:pointer" src=http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 0. Jpg"
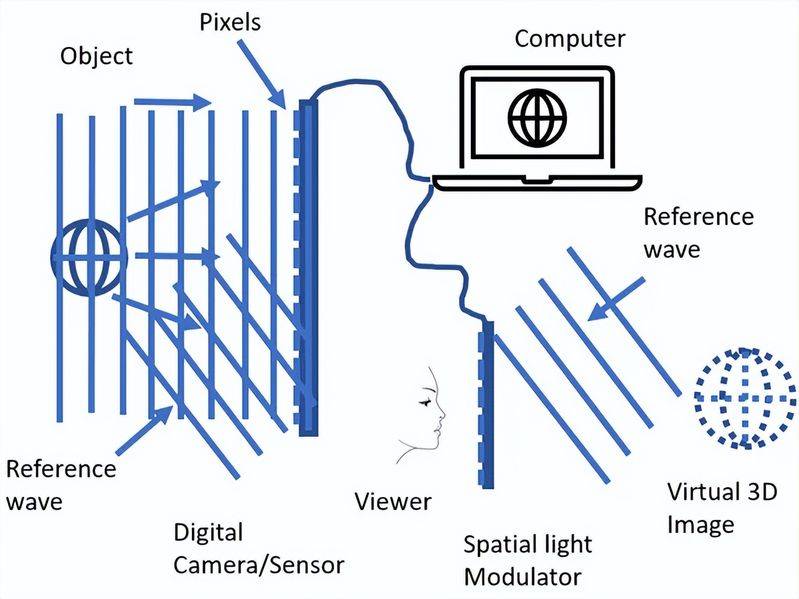
3. Design rationale analysis
The circuits consist of two main components: password locks and backup power (ups), which are set up to prevent the failure of password locks due to power outages and to save users from trouble。
Password locks include: keyboard input, password modification, password detection, locking of circuits, execution of circuits, alarm circuits, number of keyboard locks。
3. 1 keyboard input, password modification, password detection, locking and circuit execution.
Its circuits are shown in figure 1 below:
620)this. Width=620; "style=cursor:pointer" src=http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 1. Jpg"
Figure 1 keyboard input, password modification, password testing, locking, execution of circuit 3. 2 alert circuits
The function of an alarm circuit is to prevent people from opening a lock in bad faith when the password is entered for more than 40 seconds (which normally does not exceed the user input)。
The circuit consists of two main parts, two minutes of delay and 40 seconds of delay. The working method is that when the user begins to enter the password, the circuit starts two minutes, over 40 seconds, and the circuit starts 80 seconds. As figure 3
620)this. Width=620; "style="cursor:pointer" src="http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 2. Jpg"
Figure 3 alert circuits
When someone approaches the door, they touch the tp end (tp end is fixed to the keyboard, its sensitivity is very high and the circuit is guaranteed to be activated), because of the power attached to the human body, the low level of 2 ic10 feet, which causes the ic10 state to flip, its high level of output, its high level of 3 feet, the t5 connection (which can control the electrodes of t1 through r12), its yellow-lighted diode d3 from the collector pole, which means that the electronic lock is now on standby, t6 cut-off, c4 starts charging via r14 (40 seconds, at which point the user cannot enter the password more than 40 seconds, otherwise the circuit begins to alert, because the user often enters the password and knows that the password does not normally enter more than 40 seconds), and ic2 begins to enter 40 seconds late。
Start warning: when the user enters an incorrect password or enters a password for more than 40 seconds, the 2 feet of ic11 drop with the charge of c4, when the level drops to 1/3vcc (i. E. At the end of the 40-second delay), 3 feet become high (low level of the delay), through r15 (r15) to limit the conductive current of t7 to prevent the excessive burning of the tripolar tube), t7 connection, and its red-luminant d4 on the upper part of the collection pole, indicating the current state of alarm, t8 is also channeled, causing the beeper to sound, causing the thief to sound, life is weak. Call the police.
Stop alarm: when 80 seconds of alarm time have been reached, 6,7 feet of ic10 have ended c5 discharges, 3 feet of ic10 have become low level, t5 deadline, t6 transit has been forced to stabilize the compulsory circuits, 3 feet of ic11 have been exported low level, t7, t8 has been closed, the beeper has stopped alerting; or the user has entered the correct password, there is a t10 set out in the locked circuit to clear alarm signals, send them to t12 (pnp), t12 transit, force t7 radical to low level, and remove alarm signals。
3. 3 number of alarm detections and locking of circuits
The circuit will be locked for five minutes if the user fails more than three consecutive times. The working method is as follows: when the number of wire alerts exceeds three times, the 3-digit counter consisting of ic9 (74161) will produce an advance to the point where, through ic7, a zero signal will be exported to a zero end of 74161 in order to achieve a new count. Through the ic8 (and door) 2 feet sent to ic12 (555), the 3 foot produces a 5-minute high-level lock pulse (the pulse can be calculated by formula t=1. 1rc), and through the t9 reverse, the ic6 input end, the ic6 output is low, so that ic13 cannot unlock to the target of the lock. The road map is shown in figure 4 below:
620)this. Width=620; "style="cursor:pointer" src="http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 3. Jpg"
Figure 4. Warning detection and locking circuits 3. 4 second power circuits
In order to prevent power outages, ups power is provided in reserve on this circuit, which includes municipal power supply circuits, power outage detection circuits, electronic open-up concerns for electrical circuits, battery charging circuits and batteries. Its circuit chart is shown in figure 5 below:
620)this. Width=620; "style="cursor:pointer" src="http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 4. Jpg"
Figure 5 power circuits
220v municipal electricity is reduced to 12v by transformer b, which is then brought through the current bridge to complete, and 7805 steady to 5v for the electronic switching circuit, where a small transformer of 10w is selected because of the low cost of this circuit. R8, r9, r6, r7 and ic14 constitute electro-voltage comparators and, normally, v+v-ic14 output high-level flats, with the dalington tube, consisting of t3, t4, turn on the relay j, connecting the battery to the circuit, switching the power from the municipal to the battery, and ensuring the normal operation of the electronic password lock (depending on the battery capacity). Its circuit chart is shown in figure 6 below:
620)this. Width=620; "style="cursor:pointer" src="http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 5. Jpg"
Figure 6 power outage detection and electronic access concerns for circuits
T1, t2 consists of an automated charging circuit for the holding cell, which automatically stops charging after the battery is filled, of which d1 light is charging, and d2 is a job instruction. A voltage detection circuit consisting of r4, r5, t1 consists of a low battery battery voltage, and t1, t2 transports to recharge it; after full filling, t1, t2 is closed, the charge is stopped, while d1 is extinguished, and c4 is used to filter interference signals. Its circuit chart is shown in figure 7:
620)this. Width=620; "style="cursor:pointer" src="http://editerupload. Eepw. Com. Cn/fetch/20161101/328247 1 6. Jpg"
Figure 7 automatic charging circuits for batteries
In conclusion, the code of the circuit cannot be forgotten, and once forgotten, it is difficult to open it. Clk pulses using switches as 74ls112 are not very stable and can be replaced by other high-speed switches or count pulses; only 16 circuit codes can be modified, but because others do not know the number of digits of the passwords and also require the opening of the locks in a given order within the specified time frame, the chances of others opening the locks are very low. So the security code lock is still reliable。