Zhao bin
"it's not an example of a hotel camera. Rong-ho can't watch, with a cargo camera." in recent days, a video by red young-ho of the net, “war on the industrial chains”, with goods to prevent the theft of cameras, has been made available online。
Scratch, it's a chain of fire. But are these anti-smuggling devices reliable? How do we cut off the black chain
Smuggling means more than people know
In the past 2023, the topics related to the filming had been the subject of several hot searches, mostly in public places such as subways or public toilets。
But the scene is much more than public。
The name of lin zheng, who had been involved in the sale of the equipment in question, was revealed to the sino-new zealand through the vehicle. From the point of view of the equipment, modified mobile phones, car keys, glasses, watches, shoes equipped with cameras, handbags, basketball, badminton buns, skaters, crutches, etc., all of these seemingly common items can be used as a means of filming。
There was also a camera set up inside. For example, hotel rooms, usually in indoor facilities such as booths, television, dressing glasses, fire-fighting smoke sensors, lamps and even showers, are the most difficult to find in air-conditioning vents。
Web-based one-way view glass is rare in general reality because of the complexity of the installation and the ease of leaving evidence behind. The device is also easily identified, and the difference between it and ordinary glass is evident when the curtains are closed and the flashlight is placed on a mirror or glass。
Compared to the above, the following is “black technology”。
Lin zhuang described the ability of the photographer to download and call personal home cameras at any time through hacking techniques. Even our mobile phones can be controlled by hacking technology, and as long as we have a network, we can call our cameras and shoot them at any time, including all the sounds that happen around us can flow into someone else's hard drive。
Deep digging for black chains

In 2021, a report on “a needle-hole camera watching 100 people online” triggered online debate. There have been public police cases where there are illegal elements hiding needle-hole cameras in hotel guest rooms and, by sharing the app invitation code, generating 100 invitation codes per camera for 100 viewers at the same time。
There are about four players in the chain of the black industry。
Technical staff. The handling of the camera equipment, almost anything that can be fitted with cameras and batteries, can be converted into a hidden camera。
Smuggle implementer. The installation of cameras at specific locations for the purpose of filming, including real-time surveillance through virus intrusion into computer network cameras。
Processor. Collecting, collating, editing, numbering, naming, etc。
Publisher. There are also individuals. They publish video content through social media or share it with the community, attracting users to click or pay to watch。
Among the four above-mentioned roles, there are “many” jobs and one complete “industrial chain”, while illegally obtained videos are used and sold through various channels。
These precautions must be known
The poaching of industrial chains has developed a complete and complex system, followed by the counter-poaching of industrial chains。
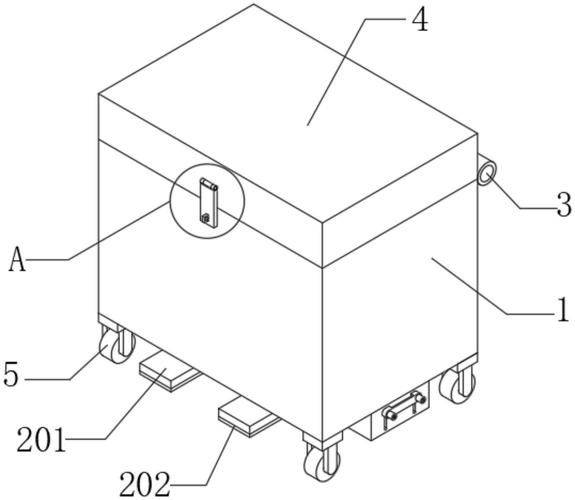
Searching for keywords such as “counter-poaching” on electric power platforms, the link to the sale of “peep-detection” equipment is “deeply invisible” in the bottom-up menu, and prices range from $15 to rmb 1150。
According to the seller, the anti-poaching equipment sold on the platform for approximately $20 could detect active cameras in a dark environment, and the equipment of $1150 was used to detect signal sources。
In interviews with the chinese new zealand as a direct vehicle, the one-song (alias) technical engineer in a well-known mobile phone brand said that ordinary cameras had activated infrared patterns in a dark environment, so that ordinary smartphone cameras could detect such cameras in an indoor dark-light environment, and there were many detailed courses on the internet. However, signal detection has no effect on the camera equipment of the plug。
Is it true that hackers can open and even call our mobile cameras at any time
Zhao hong woo, senior engineer in cybersecurity research and applications, general engineer of middle science and technology, inc., stated in an interview with china news agency that these hacking techniques are not complex. Control of personal surveillance cameras or mobile cameras is achieved through the use of approximately five means, namely, default passwords, weak passwords, network loopholes, social engineering, and cyber fishing and middleman attacks。
What are we supposed to do about it
According to zhao hongwoo, there are four technical aspects to begin with。
1. Solids should be updated regularly. The security camera solids are up to date. Manufacturers regularly issue updates to address safety gaps, which need to be periodically checked and reinforced with updates。
2. Strong passwords shall be used. Creates strong and unique passwords for camera login, avoids default passwords and selects combinations of letters, numbers and special characters, changes passwords regularly and avoids the use of guessable information。
3. Enhancing network security. Protection of family networks through strong wi-fi passwords and the use of wpa3 encryption, as well as the use of powerful and unique web passwords to limit access to the network。
4. The default settings should be changed in a timely manner upon the return of the acquisition of new networked devices. Change the default user name and password of the camera network device to avoid the default proof being used by hackers。
In general, families can prevent hacking in four ways:
The first is to observe whether the camera is acting abnormally and if the camera moves, turns or makes an abnormal sound during an irregular period of use, it can be suspected to be a sign of intrusion

(b) second, to observe the abnormality of network traffic through routers and, if there is a sudden increase in family network traffic, the camera may be hacked for remote surveillance or participation in ddos attacks
Third is the abnormality of smart home equipment, which may be the result of the intrusion of a camera and the transmission of malicious programs if there are irregularities in household equipment (e. G. Computers, mobile phones), such as automatic downloading of unknown software, eject abnormal advertisements, etc.
Fourth, the login logbook was abnormal and could have been hacked if unauthorized login records had been found。
How do we cut off the black chain
In an interview with the chinese communist party (cps) in which he was interviewed by a doctor of law at the chinese university of political science and law and a full-time lawyer from beijing city's law firm, wang yue wah, said that filming someone's privacy, even if it had not been disseminated, violated citizens' right to privacy. In the case of malicious disclosure of personal information, infringement of personal privacy and even use for illicit gain, the maximum penalty shall be imprisonment for a term not exceeding three years and a fine not exceeding seven years; imprisonment for a term not exceeding three years, arrest, control or deprivation of political rights if the offence is serious; and the dissemination or production of pornographic material if the video is taken, a photograph is disseminated and even posted on an illegal website for profit。
Wang hua reminds that the production, reproduction, publication, sale or dissemination of pornographic material for profit is punishable by imprisonment for a maximum of 10 years or life imprisonment, in particularly serious cases, with a fine or confiscation of property. Any person involved in a poaching chain may, depending on the circumstances, constitute an accomplice to one or more of the offences listed above。
The judicial authorities have never stopped striking “black chains” in accordance with the law, but why are criminal activities involving the taking of photographs being prohibited
A police officer who has been working for many years in the public security departments of the police stations and municipalities at the grass-roots level has revealed to the sino-pressing state that poaching the original equipment is easy to purchase, make simple and difficult to manage from the source. Increased communication-end regulation, such as twitter, social platforms, websites, etc., has been effective, but enormous human and material investment has made it difficult to keep this approach a secret, and it may be more effective if it starts with both the law and the camera。
First, consideration could be given to introducing relevant judicial interpretations. Further elaboration of the identification, punishment, etc. Of the conduct of the photograph and its chain. For example, there is a penalty for repeat offenders who are involved in the act of poaching but do not meet the criminal penalty criteria. The purchase and viewing of clearly hidden, private videos is also subject to appropriate accountability. It may even be possible to consider reoffending while notifying the family or the unit concerned to monitor it
The second is to hold the scenery unit responsible for the safety of its premises. Every time a customer leaves the shop, he or she routinely checks the premises of his or her own business for the presence of a camera. If it is found that a timely report is to be made, the judicial authorities will follow it up. At the same time, the public security organs regularly publicize the list of hotels found in the course of investigations and inspections with the equipment to be taken。