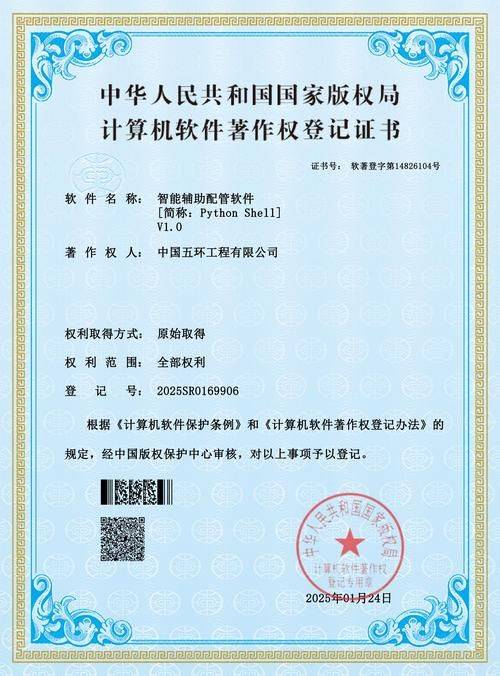
The operational manual on intellectual property protection for software enterprises, in the midst of the digital economy, places the core competitiveness of software enterprises heavily on barriers to technological innovation and intellectual property. However, risks such as “code copying” of “patent sniper” “open-source compliance disputes” in the industry are frequent, causing commercial losses at the expense of businesses and undermining the very foundations of an enterprise. The handbook combines practical experience with the legal framework, ranging from rights mapping, management systems to dispute management, provides software enterprises with landable intellectual property protection programmes and helps them to achieve long-lasting development in a balance between innovation and compliance. In chapter i, the core values of intellectual property protection in software enterprises and risk recognition 1. 1. In the financing chain, the number of patents and copyright registrations directly affect valuation; in the context of market expansion, brand barriers to trademarks and domain names can effectively intercept counterfeiters; and the protection of commercial secrets keeps core algorithms technologically superior. For example, an ai software enterprise, with more than 20 core patents, increases its valuation at the time of financing by 40 per cent and successfully discourages the technical imitation of competitions. The risk of infringement in the typical scenario software industry 1. 2 is characterized by a “chain-wide, multi-form” character: the code level: the source code in outsourcing development is leaked, the competition is stolen from the core logic (e. G. The recommended algorithm of the app of an electric power provider is reversed in reverse); the rights level: the trademarks are betched (e. G. The “xx cloud” trademark is registered in class 9 and the product cannot be properly promoted); the open-source component is used in violation of the protocol (e. G. The misuse of the gpl protocol code makes the entire software open); and the competition level: there is a malicious suit against the “proprietor” (e. G. The npe sues small and medium technology enterprises for software patents for high compensation). 1. 3 the innovative model of the logical software industry, which faces particular challenges, generates unique intellectual property issues: the double-edged sword of open-source software: the use of open-source software requires rigorous scrutiny of the type of agreement (e. G. The mit agreement allows commercial use but requires a copyright declaration, while the gpl agreement requires an open source of derivatives), and recommends the establishment of an “open-source component list” and regular compliance audit; the attribution of rights to cloud services: in the mixed scenario of saas products, in the context of “user data + business algorithms”, intellectual property ownership needs to be identified in service agreements to avoid user claims for shared rights to algorithms; copyright disputes over ai-generated codes: the use of ai-aided development requires an agreement in the labour contract that “the right to generate ai content belongs to the enterprise” and maintains a record of the development process to prove originality. Chapter ii, copyright protection guide 2. 1, copyright register: from “automatic protection” to “enhanced evidence”, we apply the principle of “automatic access” to software copyright, but the certificate of registration is the central evidence for the defence of rights (e. G., in administrative investigations, civil proceedings, the certificate of registration may directly assume the attribution of rights). The registration process needs to be aware of: material preparation: source code (recommended to submit the first 30 pages plus 30 pages of continuous code to avoid leakage of core logic; if the code exceeds 60 pages, it can be submitted for all but dissensitization, such as replacement of variable names), software instructions (required to reflect functional modules, technical features and avoid only describing interfaces), rights-attribution agreements (e. G., commissioning development required to submit a contract of assignment); submission route: submitted online through the china copyright protection centre (cppc) network of officials, or mailed/on-site to local representative offices (e. G., the beijing, shanghai, shenzhen, etc.); version management: software overlays (e. G., new core functions) should be re-registered to avoid dissimilar evidence in the event of a difference in version. 2. 2 within the copyright-control team of the development process, the attribution of rights is defined in the labour contract as follows: “software developed by an employee during his or her employment, copyrighted to the enterprise”, avoiding post-employment employee claims; commissioning/cooperative development: contracts are required to provide for “unique authorship/proportional sharing of copyright” and for “subsequently improved version” (e. G. Software commissioned, the trustee may not authorize improvements); compliance with open-source components: establishment of an “open-source component account”, recording of the name of the component, version, type of agreement, scope of use, regular scanning through tools such as “fossa” “blackduck” to avoid abuse due to a conflict of open-source agreements (e. G., an enterprise is forced to open the entire product by misusing the encryption bank of the gpl agreement). 2. 3 tort monitoring and remedy path monitoring means: through copyright monitoring platforms (e. G. The monitoring system of the copyright protection centre in china), search engine key word monitoring (e. G. The search for “xx” software breakout), tort monitoring in the application store (e. G. The mapping of apps in china, apple shops); relief options: the “patentability” of chapter iii software patent protection over the patenting of 3. 1 software is becoming more stringent and requires a “technical” core: chinese review logic: simple algorithms (e. G. The ranking algorithm), commercial methods (e. G. The internet purchase process) are not authorized, need to be combined with “technical effects” (e. G. The speed of server response, reduction of energy consumption, optimization of hardware interfaces); e. G. The “ai-based image identification software” requires an explanation of “how to optimize the gpu computing power allocation through algorithms to increase the speed of identification by 30 per cent”; overseas layout techniques: the united states and europe are more inclusive of software patents, allowing application for “calc+ hardware interaction” (e. G. The “payment verification method through mobile telephone sensors”) and 3. 2 the “preventive logic” underlying patents in patent layouts: patenting “broad protection” around core technologies (e. G., the ai large model training method, block chain consensus algorithm), with claims covering multiple dimensions such as “methods, devices, systems, computer readable media”; peripheral patents: patenting derivative technologies (e. G., fine-tuning of large models, industry-specific matching algorithms) to create a “proprietary network” to intercept competitions; risk avoidance: regular “patent search” analysis, competition patents, “negotiation design” of potentially abusive technical routes (e. G., adjustment of algorithm steps, replacement techniques). 3. 3 detailed applications for patent applications and maintenance are written: claims need to be “simple and broad” (e. G., “server” summarized as “calculating equipment”) supported by “specific implementation cases” (e. G., steps to describe algorithms, hardware interaction); it is proposed to entrust “professional agents in the field of software” with the avoidance of patent invalidity as a result of drafting defects; review responses: reviews of “lack of creativity” need to highlight “technical improvements” (e. G., where existing technology is a single-line process and the invention is a parallel multi-line process, increasing efficiency by 50 per cent); patent maintenance: the establishment of a “patent value assessment system” may be considered for waiver of patents that have no commercial value for three consecutive years (e. G., avoiding high annual fees); and core patents may be countered through a “proprietary avoidance” torance action against competitions (e. G., where an enterprise uses an invalid other party's base of patents, winning torts). (a) chapter iv: "all-dimensional defence" defence registrations registered in the 4. 1 trademark of the software trademark and domain protection system: registration of "approximate graphic" "english translation" of the trademarks (e. G. "xx cloud" registration of "xxyun" "x clouds"); in the case of plans to go out to sea, pre-registration is required in the target countries (e. G., the united states, the european union, south-east asia) and the process can be simplified through “madrid international registration” (submitted within six months of the date of registration of the chinese trademark). 4. 2 compliance of the "brand harmonization" 4. 3 trademarks and domain names protected by domain names with trademark marking norms: when using a trademark in a software interface, promotional material, it is necessary to mark “single” (registered) or “tm” (in the application) and to ensure that “marks are consistent with the registration certificate” (e. G., a word trademark is registered, no graphics may be added to it); compliance with domain name interpretation: avoid jumping through domain names to perform “fiction”; if a tort domain name is found to be used by another person, a complaint may be filed with a domain name registerer (e. G. Aliyun, twirling cloud) to request a suspension of the interpretation. Chapter v, on the systematization of commercial secrecy, establishes the “three elements” of 5. 1 business secrets that need to be met simultaneously: confidentiality: not known to the public (e. G. Source code is open only to research and development teams and “confidential agreements” are concluded with the outside world); value: economic benefits (e. G. A core algorithm that increases market ownership of products by 20 per cent); confidentiality: reasonable confidentiality measures (e. G. Physical isolation, technical encryption, institutional constraints). For example, a financial software enterprise has classified core wind algorithms as business secrets, effectively preventing leakage through measures such as “access rights rating” (only the core team can view the complete code), “code encryption storage” (using aes-256 encryption), “separation audit” (recycling equipment, removal of permissions)。5. 2 physical and technical measures of confidentiality measures: development of physical isolation of the environment from the offline network (e. G., development of servers without internet access, access through springboards); source code encryption (encrypted warehouse using the “gitlab enterprise version”, or self-research encryption tools); document watermarks (adding “internally confidential” watermarks in technical files, indicating access to personnel information); regime and contractual constraints: development of the commercial secrets management scheme, specifying “secret scope, duty of confidentiality, penalty for non-compliance”; confidentiality agreements with employees, agreement on “secretity obligations for two years on duty and after separation” and accompanying “competence restraint agreements” (requirements to be paid); and confidentiality contracts with partners (e. G., contractors, suppliers) to clarify “secret content, confidentiality period, liability for breach of contract”. 5. 3 combined “criminal + civil” administrative and criminal remedies for violations: reporting to the market regulatory authority (formerly the business sector) that the violation “losses the rights holder more than $500,000” or “revenues more than $300,000” may be reported to the public security authorities (article 219 of the criminal code “offences against business secrets”); civil proceedings: requiring the infringer to cease the violation, compensation for the damage (the loss may be calculated by reference to “costs of research and development, loss of profits, reasonable defence costs”) and, in the case of breaches of confidentiality by employees, liability for non-compliance. Chapter vi on the formation and optimization of the 6. 1 organizational structure and division of responsibilities of small and medium-sized enterprises (smes): an “ipr commissioner” may be established, attached to the legal or r & d department, responsible for day-to-day registration, monitoring and defence of rights; large enterprises: it is proposed that a “ipr” be established and that the “ipr group” be established, with the “market group” of the “proposal rights group”, in collaboration with the r & d, the market, and the financial sector (e. G. Prior to the development of a project, the ministry of intellectual property is required to conduct patent searches). 6. 2 the development of a project phase of a full-process management mechanism: conducting a “patent retrieval analysis”, mapping the risk of infringement of technical routes, while also exploring innovative points (e. G., identifying patentable directions through a “brainstorm + patent database analysis”); the development phase: identifying “right attribution” (e. G., contract contracts commissioned for development, compliance audits of open-source components), periodically conducting “authorization registration” (e. G., quarterly updates); the listing phase of products: conducting “intellectual property review” (e. G., whether trademark use is regulated, patents cover core functions) and producing “intellectual property inventory” (e. G. Patent number, copyright registration number, trademark registration number) along with product publication; the marketing phase: establishing “infringe mechanism” (e. G., monitoring intellectual property rights dynamics of competitions through “business check” and monitoring of brand abuse information through “business check”). 6. 3 in-house training and cultural construction stratification training: training of r & d personnel on “patent mining and circumvention design”, training of market personnel on “mark compliance and brand protection” and training of the entire staff on “business secrecy awareness”; innovation incentives: creation of an “intellectual property incentive fund” (ipr incentive fund) to award bonuses (e. G. $5,000 per case after patent authorization) to teams that submit patent applications and register copyright rights, and promotion opportunities to employees who avoid the risk of major abuses; cultural penetration: incorporation of “intellectual property compliance” into corporate values, emphasis on the importance of intellectual property protection at the time of entry, start-up of projects, and the creation of a “reventive and abusive” culture. Chapter vii disputes should deal with “step-by-step” consultations and warnings to extend 7. 1-to-violation disputes to international protection: a letter of attorney should be sent to the infringer to clarify “tort facts, legal consequences, conditions for settlement” (e. G. A request for cessation of tort, compensation for damages), and some cases could be resolved by negotiation (e. G., an enterprise compelling the competition through a letter from a lawyer to avoid litigation); 7. 2 international protection of the “breeding strategy” of international intellectual property rights: through the “bolney convention”, software should be automatically protected in member states, but a “authority registration” could be recommended in the target country (e. G., registration with the united states copyright agency, which could serve as a prima facie evidence of rights protection); the international patent board: by “pct international application” (submitted within 12 months from the date of priority), to countries/regions such as the united states, the european union, japan and to avoid litigation of “national standards” (e. G., the united states allowed software patents, together with technical effects); and the “collectortor” of the joint industry 7. 3 a typical case of “experimental extraction” open source tort: an enterprise has been sued by the open source community for failing to comply with the “open source of the open source derivatives” requirement by using the open source code of the gpl agreement, and has been forced to open the product and compensate for its loss. Lessons learned: establishment of an audit mechanism for compliance with open-source components; patent sniper case: an ai company was sued by npe for “image identification patent” and won by “invalid counterparty patent” (proven patent lack of creativity). Experience: periodic patent retrieval, pre-packaging of invalid evidence; commercial secrecy case: