The reason why this article was written was simply to make wifi safe and to provide a broad direction for the infiltration test beginners, especially for the tester of wireless penetration。
I listed seven popular wifi hacking tools:
• fernwifi wirelesscracker
Insider
• kismac
- kismet
• mI don't know
• netstumboller
• wifiphisher
If you are interested in the above tools, you can contact them, and we will discuss them in detail, depending on the level of interest, in a decentralized and detailed way, including software presentations, implementation steps, basic operations, etc。
Since multiple attack media can be deployed, breaking the wireless code is not a very difficult hacker attack. So far, weak or default passwords have been the easiest way to access routers and networks. A simple search triggered thousands of videos on the subject, some of which did well
Okay, you should understand that the world's easiest and successful wifi hacker is making sure you have access to routers。
This article is aimed at beginners, so let's confirm some terms and take an inventory:
Sniffing/ eavesdropping:
This term indicates that you pass all data through hacker computers first and passively listen to network data without user recognition。
Intermediaries attack:
The attack, usually abbreviated by mitm, was used to intercept traffic between user equipment and target systems, such as the provision of wi-fi hotels and to make the victims ' machines perceive hacking machines as normal equipment。
Dns cache poisoning:
A common method of attack is the use of web data by hackers to divert traffic to the destination they choose。
Rogue access point/rogueap:
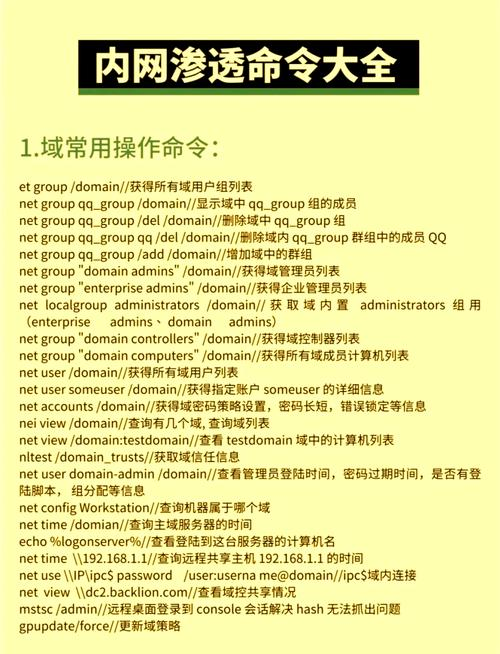
Wireless access points installed on company networks. These access points are on legitimate networks, but hackers carry out and intercept data during intermediate attacks。
Unsafe wi-fi network:
Unsafe wi-fi is a wireless network that does not require users to log in using user names and passwords. Usually displayed as an open network。
Wep:
The first wireless security programme is designed to provide essentially the same security as the privacy enjoyed in the cable environment. This is the least usable type of wireless network。
Interim key integrity protocol (tkip) used by wpa:
The agreement further enhanced the security of wep without the need to purchase new hardware. It still uses wep for encryption, but it makes it more difficult and time-consuming to crack the wep attack。
Wpa2-psk:
This is the next level of wpa, designed for families and small businesses. By definition, the new version uses the pre-shared key (psk). This has become the standard now used by most families today。
Wpa2-aes:
This is the wpa2 version used by the company. It uses advanced encryption standards (aes) to encrypt data and is the safest. It usually coincides with the radius server dedicated to identification。
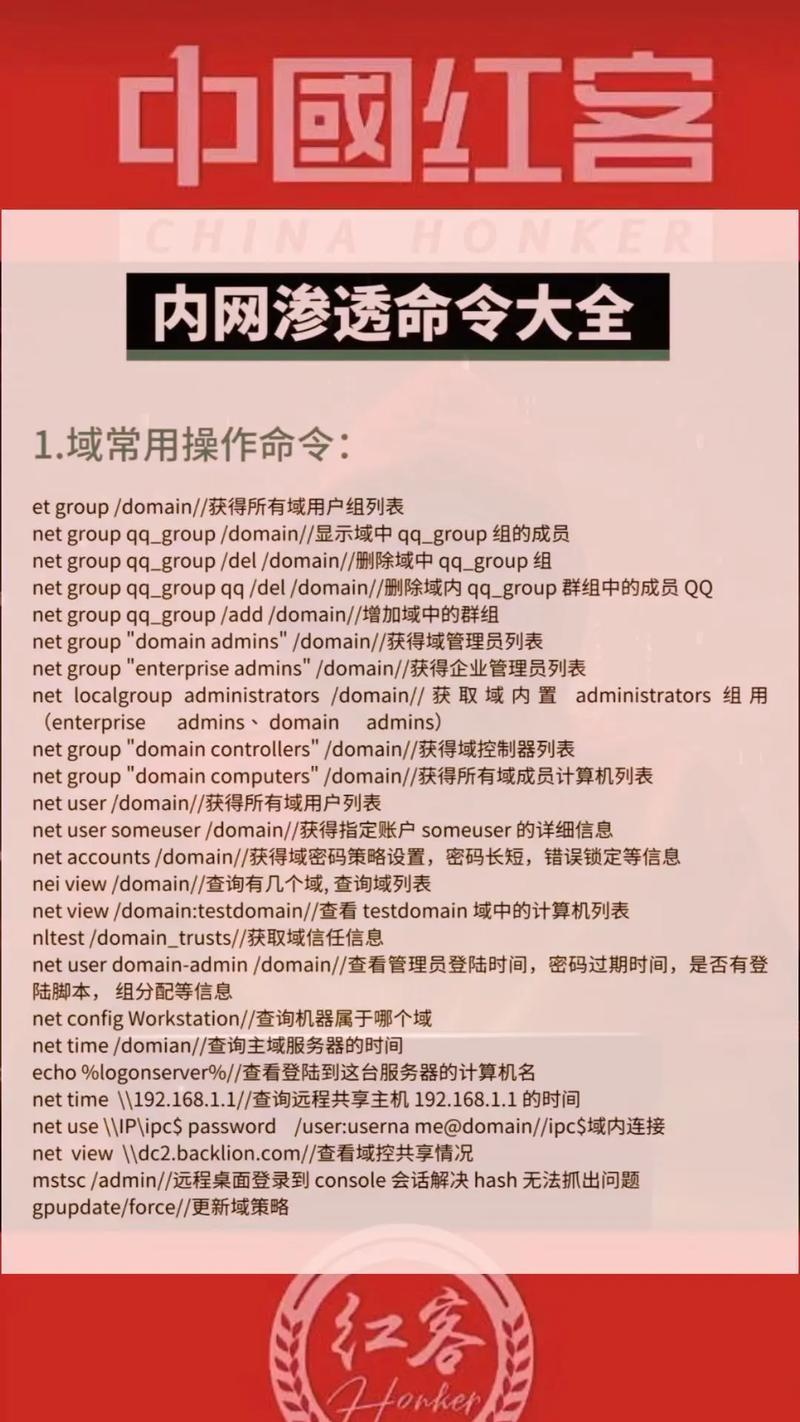
Radius remote identification dial-in user service (radius):
A network agreement that provides centralized identification, authorization and accounting management for users connected to and using network services within the enterprise. These users are identified through corporate systems to obtain additional protection。
Channel:
Wireless networks use separate channels so that traffic streams do not interfere with each other. 802. 11 wireless standards allow channels from 1 to 14。
Violent attacks:
A hacker tries to break the code by constantly trying to log in using different documents until a valid one is found. This may take hours, days or months, depending on the complexity of the password used。
Dictionary attack:
A method used to query and break the password of the user or wireless device by browsing through all words in the dictionary, in turn trying each word until a valid password is found。
Vpn:
Vpn is a means of using the public internet, such as a secure dedicated network. It encrypts data and routes them through remote servers to keep activities and positions confidential and secure。