3. Forced mobile phones to recover passwords in time for an accident
4. Be vigilant when receiving mail related to personal information and money (e. G. Winning, collecting funds, etc.)

How to protect social networking from leaking information
1. Do not easily click unverified chains answer
2. Not to publish personal information on social networks
3. Do not register freely on the internet and register accounts according to their needs
4. Using security and privacy settings on social networking sites to protect sensitive information

How to prevent the virus, the carp attack
1. Installation of formal anti-virus software to update the virus on a regular basis library
2. Downloading and installing software into the software network down load
3. Timely updating of computer systems and installed software to prevent security leakages hole
4. When using a mobile storage medium, kill and turn it on, and not put the device on an unsafe computer
5. Password computer system accounts to prevent physical transmission of viruses
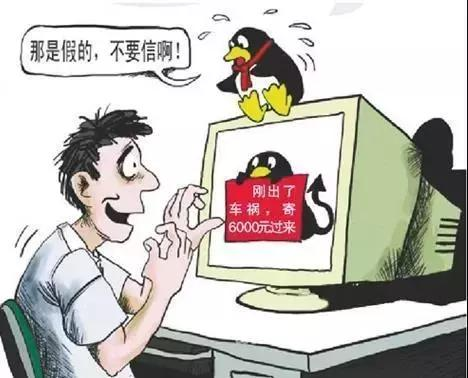
Prevention of cyber-fraud
One, don't easily believe in part-time work on the internet
2. Don't transfer money easily to anyone claiming to be a substitute for microbusiness
Three, any person who calls and texts you, and then makes you transfer money is a liar

Civilization internet initiative
Be good at online learning and stop browsing bad information
Appropriate use should be made of online resources, drawing on scientific and cultural knowledge, browsing at effective health information, identifying good and bad on the internet, and consciously resisting all kinds of false and negative content, so as to “no faith, no rumours”
Maintenance of cyber security and non-interference
The importance of cybersecurity should be fully recognized, with strict requirements for rational and legitimate use of network resources, the elimination of cyber security hazards, the enhancement of cybersecurity awareness, the monitoring and prevention of insecurity, the maintenance of normal network operations and the promotion of healthy network development
Good physical and mental health
There should be controlled internet access, good use of internet technology to obtain useful information, solve problems in learning, rationalize access times, and not become addicted to networks, affect normal learning life and damage physical and mental health
Maintaining cyber-ethics and eliminating the vices of the internet